The new era of cloud security
As cloud ecosystems mature, it is becoming evident that the same platforms, technologies, and services that make the cloud so powerful can also become a source of vulnerability. A growing concern among security leaders: how can our investments in cloud work for us?
A June 2020 IBM Institute for Business Value (IBV) study found that nearly 90% of cloud spend is devoted to either public or hybrid clouds, and 40% of overall workloads operate across multiple clouds. Our approach to security operations must adapt to these new ways of working, where perimeters and trust are negotiated in real time.
More than 80% of executives consider security a brand attribute that differentiates their organization.
This report explores how cloud infrastructure, technologies, and services are transforming cybersecurity operations. We asked 930 security and business leaders from 17 industries and 20 countries to assess their cloud operations from two perspectives. First, how rapidly are their organizations migrating business operations to cloud and, second, what is the relative maturity of their cloud security operations? We used this data to better understand if cloud security capabilities are keeping up with cloud migration.
This report's chapters present our findings from three key perspectives:
- Understanding the risks
- Shifting the security paradigm
- Re-envisioning security as a value driver
Ecosystems evolve: Re-orienting around a shared responsibility model
In response to an ever-expanding threat landscape, security operations are evolving from a traditional emphasis on threat mitigation to more holistic concerns like cyber resilience. Cyber resilience addresses the entire security lifecycle in a comprehensive and systematic way, as a series of interlocking capabilities designed to enhance the organization’s overall security posture.
Accompanying the shift to cloud-centric operating models, data and operations are increasingly federated across partners. Threat actors are targeting strategic partners, and as a result, threat vectors are extending out from the individual organization to the shared ecosystem.
Organizations with the most mature cloud security practices outperform peers by more than 2x in terms of both revenue growth and profitability.
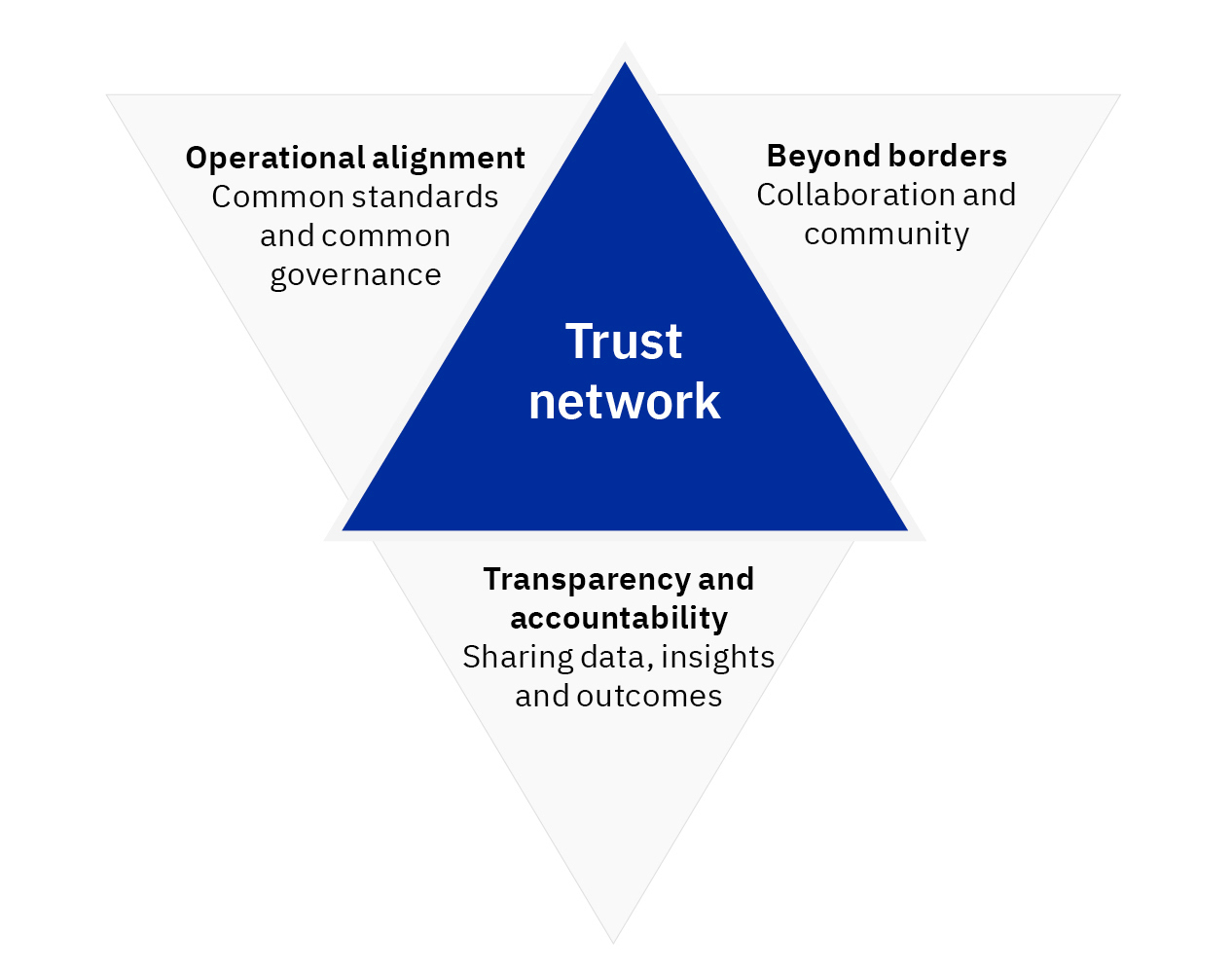
Today, cloud ecosystems are vulnerable because visibility is limited. Trust actors share resources to create value. But they typically share insights or governance on an ad hoc basis, after the fact. Threat actors use these gaps to probe for vulnerabilities and to undermine trust. They coordinate operations and share information to maximize leverage. For trust actors, the lack of ecosystem-wide cyber awareness and response capabilities degrades cyber resilience and puts value-realization at risk.
Cloud enables security leaders to re-orient their security operations around a more collaborative security model—one that is optimized for shared responsibility, mutual accountability, and collective resilience. By prioritizing visibility, sharing, and common governance, leaders open the door to new value propositions that extend beyond organizational boundaries.
The trust network advantage: Greater accountability and information sharing across the ecosystem enhances cyber resilience for all parties
Read the full report to learn how mature cloud security practices can help your organization strengthen cyber resilience, drive revenue growth, and boost profitability.
Meet the authors
Dr. Shue-Jane Thompson, Vice President and Senior Partner, Security Strategy and Growth, IBM ConsultingShamla Naidoo, Vice President and Managing Partner, IBM Security
Shawn DSouza, Global CTO, Hybrid Cloud Services, IBM Consulting
Gerald Parham, Global Research Leader, Security and CIO, IBM Institute for Business Value
Download report translations
Originally published 23 March 2021


