Partner with IBM Security Services to help your transformation journey.

Having cybersecurity keep up with the pace of innovation is a challenge many organization leaders like you face. You need an approach that manages current and anticipated risks without adversely affecting the progress of your business growth. A clear and aligned strategy to assess your enterprise’s overall maturity and gaps is necessary for you to build security into your digital strategy and transformation initiative. Without such a strategy, you may question if and how you can effectively respond to threats that continue to grow exponentially.
Your fears are well founded. These figures indicate just how data breaches have become all too common and too costly for enterprises like yours when not addressed.
USD 3.86 million
Global average total cost of a data breach in 20201
USD 871,686
Global average for theft of credentials in 20192
2,000%
Growth of attacks on operational technology between 2018 and 20193
Get more information on the security landscape by reading the 2021 Threat Intelligence Index Report.
Cybersecurity is a top priority due to several other mounting pressures.
Over the past decade, the cloud has become integral to nearly every digital and business transformation strategy. With broad adoption of hybrid multicloud, microservices and integration of cybersecurity into the DevOps lifecycle, the perimeter has almost completely dissolved, leading to an even greater importance placed on the security function.
You need to decide how to select and integrate any on-premises and software as a service (SaaS) security tools that you already have with the appropriate native cloud security controls provided by cloud service providers. However, this process often results in a fragmented patchwork of solutions with limited cohesion and visibility.
- 80% of workloads have still not yet migrated to cloud4
- 94% of enterprises have multiple clouds5
- 60% of companies use 25 or more unique security products, with 44% engaging more than 10 vendors6
Organizations worldwide face increasingly destructive attacks. Malware, such as ransomware attacks, continue to plague businesses and governments. Insider threats and compromised credentials are difficult to detect and mitigate.
Piecing together several seemingly low-risk events to find the one extremely high-risk cyberattack requires technology and skill. Data exfiltration events, such as insertion of Universal Serial Bus (USB) devices, use of personal email services, unauthorized cloud storage or excessive printing, need to be controlled.
- 67% increase in ransomware attacks alone in 20197
- 280 days to identify and contain a data breach8
- Top three initial attack vectors are compromised credentials, cloud misconfiguration and vulnerability of third-party software9
Fines from violations of the General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA) and other privacy laws can potentially cost billions for global enterprises. Data privacy protection concerns are driving new regulations around the world. Organizations are trying to protect data privacy online and improve personal data protection. Enterprises that exceed the new requirements may be able to build trust with consumers and users and stand out from their competitors.
It’s important to evaluate your existing security governance — including data privacy, third-party risk and IT regulatory compliance needs and gaps — against your business challenges, requirements and objectives.
- The Federal Trade Commission (FTC) imposed a $5 billion penalty and sweeping new privacy restrictions on Facebook10
- Compliance failures is one of the top four data breach cost amplifiers11
An organization is only as strong as its people. For cybersecurity leaders, the challenge of recruiting and retaining the best technical and business professionals is a constant worry. There’s continued high demand for cybersecurity professionals and an ongoing shortage of talent.
The security industry is facing a shortage of qualified candidates with the necessary hands-on skills and product experience. Those working as security professionals need continuous training and professional development to keep up with evolving technologies and the threat landscape. They’re also challenged to find time to properly mentor and train new hires.
- CISOs will face an estimated 1.8 million unfulfilled cybersecurity jobs by 202212
- Security skills shortage is a top three data breach cost amplifier13
- USD 2 million higher cost of an average data breach of those organizations without incident response teams and testing compared to those with no IR team and plan testing14
An increased prevalence of threats exists for mobile devices, edge computing, operational technology (OT), Internet of Things (IoT) and Internet of Medical Things (IoMT). New connected devices can introduce vulnerabilities into the most secure environments and can expose critical data and systems to an attack.
Security assessment of your network and how these devices interact is critical. The devices themselves should be tested to identify default passwords, misconfigurations, unsecured connections and security controls. Centralize monitoring for OT, IoT and IoMT devices to identify abnormal activity and potential threats.
- 38+ billion IoT connected devices in 202015
- 76% of respondents said remote work would increase time to identify and contain a breach16
- 2,000% growth of attacks on operational technology between 2018 and 201917
In response, many enterprise leaders like yourself know they need to emphasize cybersecurity proactively. The top challenge is having to use too many tools from too many vendors.
63%
of enterprises see cybersecurity as a business enabler
42%
of enterprises include cybersecurity in the planning of all new deployments
83%
of enterprises have no plans to reduce their cybersecurity budgets, despite the decrease in IT spending caused by COVID-1918
Additionally, hard-to-manage cybersecurity portfolios are the main inhibitor of security capability improvement.19
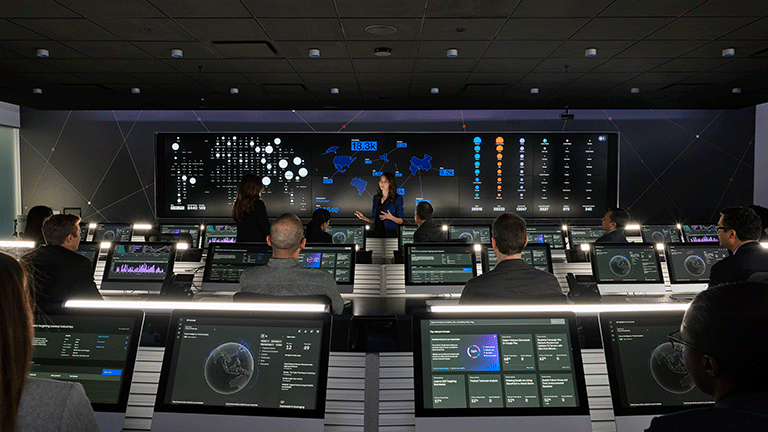
The answer to all of these challenges is IBM® Security Services, which provides the modern, open, unified approach to security that you need.
With IBM Security Services, you get proactive help to align, protect, manage and modernize your security in the following ways:
- Align your security strategy with your business.
- Protect your digital assets, users and data.
- Manage your defenses against growing threats.
- Modernize your security with an open, multicloud strategy.