With the US National Institute of Standards and Technology (NIST) post-quantum cryptographic standard expected to be published this summer, companies need to start navigating the migration to quantum-safe cryptography. The most sustainable and effective way to make cryptosystems resilient for the quantum era is to establish cryptographic agility, or crypto-agility for short.
Crypto-agility means that a system, platform, application, or organization can rapidly adapt its cryptographic mechanisms and algorithms in response to changing threats, technological advances, or vulnerabilities. However, what crypto-agility looks like in practice is less obvious. Crypto-agility is not just about transitioning to quantum-safe cryptography in the nimblest way possible, and it’s not something that can be achieved merely by updating encryption algorithms and protocols. Instead, you need to adapt your organization’s cryptographic architecture, automation, and governance to allow for greater control and flexibility as you work to anticipate evolving cyber threats efficiently and with minimal disruption.
Why is crypto-agility important?
New quantum-safe cryptography standards will continue to emerge along with new regulations for security protocols as quantum computing technology advances. Therefore, you must be able to quickly locate and update cryptography across your IT landscape to address emerging cyber threats and vulnerabilities. That means understanding where cryptography is deployed across all the dependent components in a system and how it is implemented in each component. For example, a Java application containing sensitive client data may be built using the Java language, but it will contain many third-party dependencies that contain cryptography, such as a Java framework, a Java virtual machine, a database component, remote APIs, the operating system, and the hardware on which it is deployed. Each of these components may integrate cryptography differently, making it important to understand cryptography usage in the context of system dependencies.
Crypto-agility also manifests at the level of algorithm design and assurance. Cryptography providers should ensure that there are different algorithm implementations for different security strengths and that the algorithms dynamically scale in security strength based on configuration. But most problems result from flaws in the algorithm implementations themselves. For example, block ciphers are susceptible to implementation flaws through the improper use of their mode of operation, or the algorithm that cryptographically transforms the data based on the block cipher. Implementation flaws can also result from misusing cryptographic primitives, such as by improperly combining them in protocols. Therefore, you need to maintain ongoing visibility into your cryptographic ecosystem so that you can identify potential cryptographic weaknesses and remediate them quickly.
The principles of crypto-agility can give you greater control over the configuration and deployment of cryptography by abstracting and simplifying the way you interact with it. Rather than settling for cryptographic components that use low-level cryptographic APIs, you can work toward using application interfaces, design patterns, microservices, and policy configuration frameworks that facilitate migration across implementations. These interfaces should also properly handle the challenge of programming language bindings — libraries that serve as a bridge between different programming languages to enable a library to be used for a different language than the one it was written for.
Lastly, crypto-agility drives alignment between stakeholders within the enterprise and across the cryptography life cycle. Cryptography researchers, providers, and consumers can work together to create more responsive cybersecurity architectures through a shared focus on creating structures that make cryptography implementations flexible and scalable. As an added benefit, this reduces the chances that cryptographic libraries and algorithms will be misused.
Building crypto-agility might seem like a significant undertaking, but the quantum-safe migration is the perfect time to begin this work. Regardless of your organization’s current level of security maturity, you can use a framework centered on architecture, automation, and governance to establish crypto-agility in and beyond your transition to quantum-safe cryptography.
Crypto-agility requires modularity and abstraction
When NIST announced its program to solicit, evaluate, and standardize post-quantum cryptographic algorithms in 2016, it prompted organizations to begin considering what quantum-vulnerable cryptography they might be using.In 2021, the Department of Homeland Security released a memo on “Preparing for Post-Quantum Cryptography” directing operational and support components to identify and inventory systems that use public-key cryptography. In 2022, the White House issued a National Memorandum (NSM-10) requiring federal agencies to provide annual inventories of their cryptographic methods and quantum-vulnerable systems, starting in May 2023. These efforts revealed that locating cryptography within business applications is like searching for a “needle in a haystack,” and tracking it down across the supply chain can prove even more difficult. If you can identify it in third-party components, you rely on the provider to make the necessary changes.
Cryptographic discovery can require a lot of time and resources. A more agile cryptographic infrastructure would simplify this process in the future by centralizing and abstracting cryptography so that you can monitor and update it without digging into application code. This entails decoupling cryptography from applications, instead driving configuration from middleware, sidecars, and/or platforms. An agile cryptographic architecture also employs modularity through abstraction layers, isolating the applications, systems, and network from specific cryptographic implementations. This, in turn, allows systems to support multiple encryption algorithms and providers interchangeably. For their part, cryptography providers can promote crypto-agility by transitioning from cryptographic libraries to services, engines, and sidecars.
Crypto-agility requires automation
A crypto-agile framework also means using automation to dynamically manage cryptographic parameters, encryption, keys, and certificates across the IT landscape. Automation tools and scripts can handle tasks like key generation, rotation, and updating cryptographic settings based on predefined policies or events. This helps organizations develop operational agility as they adapt cryptographic implementations to accommodate changing security requirements.
Moreover, managing cryptography within a framework of crypto-agility entails centralizing the routine collection of cryptographic metadata and usage logs. Automating these processes enables you to detect potential vulnerabilities in real time and maintain continuous compliance.
Crypto-agility requires governance
Cryptographic governance is just as critical to crypto-agility as building more efficient configuration and management processes. Governance requires the ability to understand where and how cryptography is used, as well as the ability to initiate and monitor changes. Most of the cryptography that organizations use is in third-party components and applications, making it essential to include the supply chain in the governance scope. Standards such as the Cryptography Bill of Materials (CBOM), now included in the CycloneDX 1.6 standard and supported by IBM Quantum Safe Explorer, can be used to help understand and govern the supply chain.
Within every organization, CISOs, security architects, DevSecOps engineers, application developers, and other stakeholders should align on the definition and enforcement of policies related to cryptographic algorithms and practices. This team should work together to create a system for adhering to industry standards, selecting appropriate cryptographic algorithms based on security needs, ensuring compliance with regulatory requirements, and updating or retiring outdated cryptography. Much of this work can be centralized in a Cryptographic Center of Excellence (CCoE), where a cross-functional team collaborates to promote awareness and training in the latest standards, review proposed cryptographic architectures, and develop policies that support agile design patterns and dynamic cryptography management. An internal CCoE can then align with industry- and association-backed centers of excellence, such as the NIST Cybersecurity Center of Excellence (NCCoE), to explore the latest guidance on and use cases for cryptographic implementations and remediation patterns.
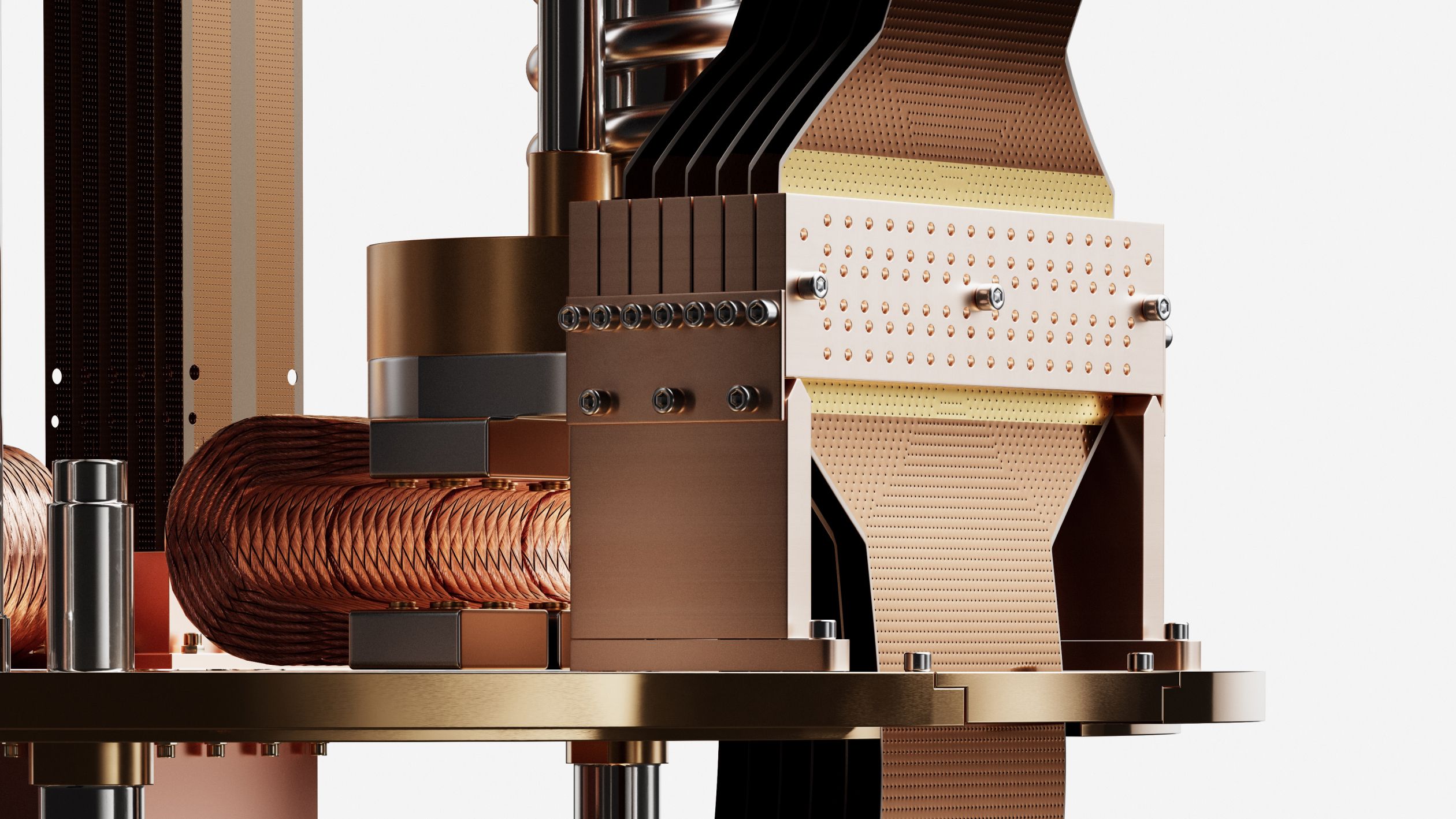
How IBM Quantum Safe can help you build crypto-agility
To help you establish crypto-agility throughout your quantum-safe journey, we developed IBM Quantum Safe technologies that build simplicity, flexibility, and automation into your quantum-safe transformation roadmap.
With our discovery and observability tools, you can locate cryptographic artifacts in data at rest and data in transit. IBM Quantum Safe Explorer identifies cryptography across portfolios of applications, analyzes dependencies, and creates a cryptographic inventory. Our quantum-safe cryptographic posture management tool further supports operational agility. By automating metadata aggregation across the entire enterprise IT landscape and providing policy-based vulnerability identification that integrates with your ticketing system, you can monitor and strengthen your cryptographic posture as your modernize your broader cybersecurity infrastructure. This, in turn, supports a more robust governance model that enables stakeholders to monitor compliance, track remediation progress, and make better informed policy decisions.
As of May, organizations can take a major step toward building a more agile cryptographic architecture using the adaptive proxy utility offered through IBM Quantum Safe Remediator. This network remediation tool enables you to position an intermediary between all client types and your business applications. The tool supports classical, quantum-safe, and hybrid forms of cryptography, allowing you to migrate heterogeneous infrastructures in a step-by-step and agile fashion that minimizes business disruption. The adaptive proxy also collects metrics so that you can track your organization’s progress along the quantum-safe journey. Additionally, IBM Quantum Safe Remediator provides a performance test harness utility that enables you to test various combinations of quantum-safe cryptographic algorithms. Using this capability, organizations can understand the impact of different post-quantum algorithm combinations on their infrastructure and select the best migration approach.
IBM Quantum Safe fosters agility throughout every step of the migration to quantum-safe cryptography. Whether you are just beginning the cryptographic discovery process or are already well into the transition to post-quantum cryptography, we will support you with the tools, approaches, and strategies you need to create your quantum-safe future. Start building crypto-agility today by identifying and inventorying your cryptographic assets, establishing a governance model to monitor and strengthen your cryptographic risk posture, and incrementally transitioning to quantum-safe cryptography while building a stronger, smarter cybersecurity framework for the quantum era.