Registering a gateway service
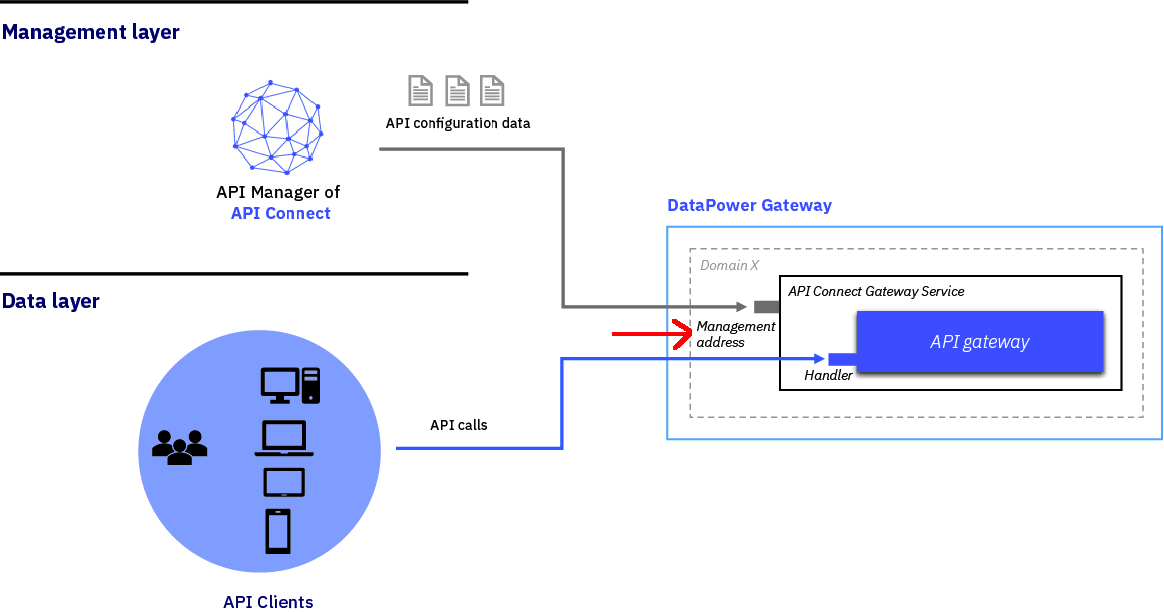
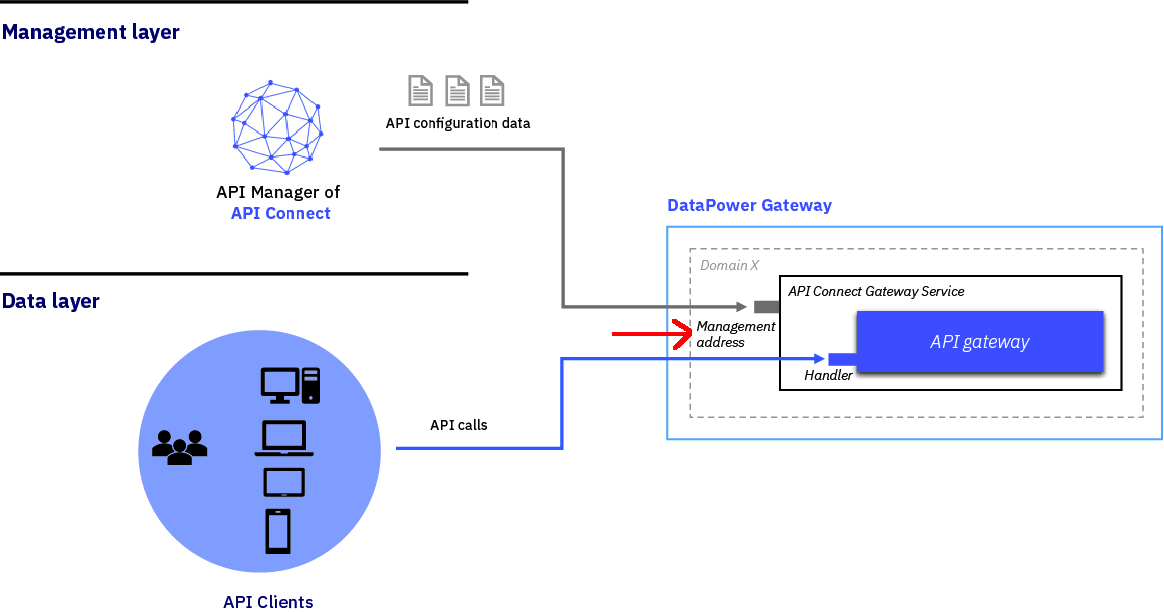
A gateway service is required to handle incoming traffic for APIs.
Before you begin
Also complete the following task:
About this task
A Gateway service represents a cluster of gateway servers that host published APIs and provide the API endpoints used by client applications. Gateways execute API proxy invocations to backend systems and enforce API policies including client identification, security and rate limiting.
One of the following roles is required to register and manage a gateway services:
- Administrator
- Topology Administrator
- Owner
- A custom role with the
Topology:Managepermission
Note: You can also register, and manage, gateway services by using the developer toolkit CLI; for details, see
apic
gateway-services.
Procedure
Complete the following steps to configure a Gateway service for your cloud:
| Field | Description |
|---|---|
| Title (required) | Enter a descriptive title for the gateway service. This title will be displayed on the screen. |
| Name (required) | This field is auto-populated by the system and used as the internal field name. |
| Summary (optional) | Enter a brief description. |
| Management endpoint on the gateway service: Endpoint (required) | Enter the API Connect Gateway Service endpoint.
|
| Management endpoint on the gateway service: TLS client profile (required) | Specify the TLS Client profile to use when contacting the gateway through the management
endpoint. Note: The default value is Gateway management client
TLS client profile:1.0.0. If you are using a DataPower Gateway in a Kubernetes
deployment, with mutual TLS enabled, use this setting. For any other gateway, if the gateway is not
configured with the correct TLS credentials the gateway registration will fail with this setting. To
prevent registration failure, select either Default TLS client profile:1.0.0
or your own custom TLS client profile. For information on configuring a custom TLS client profile,
see Creating a TLS Client Profile.
|
| API invocation endpoint: API endpoint base (required) | Enter the base portion of the URL that maps to the base portion of the URL for incoming API traffic. It is a public FQDN with additional paths that are specific to your API calls. For example: https://api.mycompany.com |
| API invocation endpoint: Server Name Indication (SNI) - Host name | For supporting Server Name Indication (SNI) at the API Endpoint Base. The default hostname
of '*' is required to allow all hosts. Enter other host names as needed. Wild card format is
supported. The SNI capability enables you to serve multiple TLS secure host names through the same
Gateway service, using the same IP address and port, without requiring them to use the same TLS
profile. Note: To allow requests from clients that don't support SNI, you must include a host
name value of '*'.
|
| API invocation endpoint: Server Name Indication (SNI) - TLS server profile | The TLS server profile that supports the given hostname for SNI. |
| OAuth shared secret (optional) | For sites using native OAuth providers, enter the shared secret that will be used by all
API calls going through the gateway. Note: The specified shared secret must be 64 characters (64
bytes) in length, prefixed with
0x, and must consist only of hexadecimal
characters. For example:
0xa354282f227c10250511ae9c9e8c7ed9f4f1bd0d7c04cb6d5bd178f8c62296e3 |
The following diagram illustrates the gateway service connection: