
- Security Services and Remediation
- Security Assessments
- Assets and Tools
- Current Asset Versions
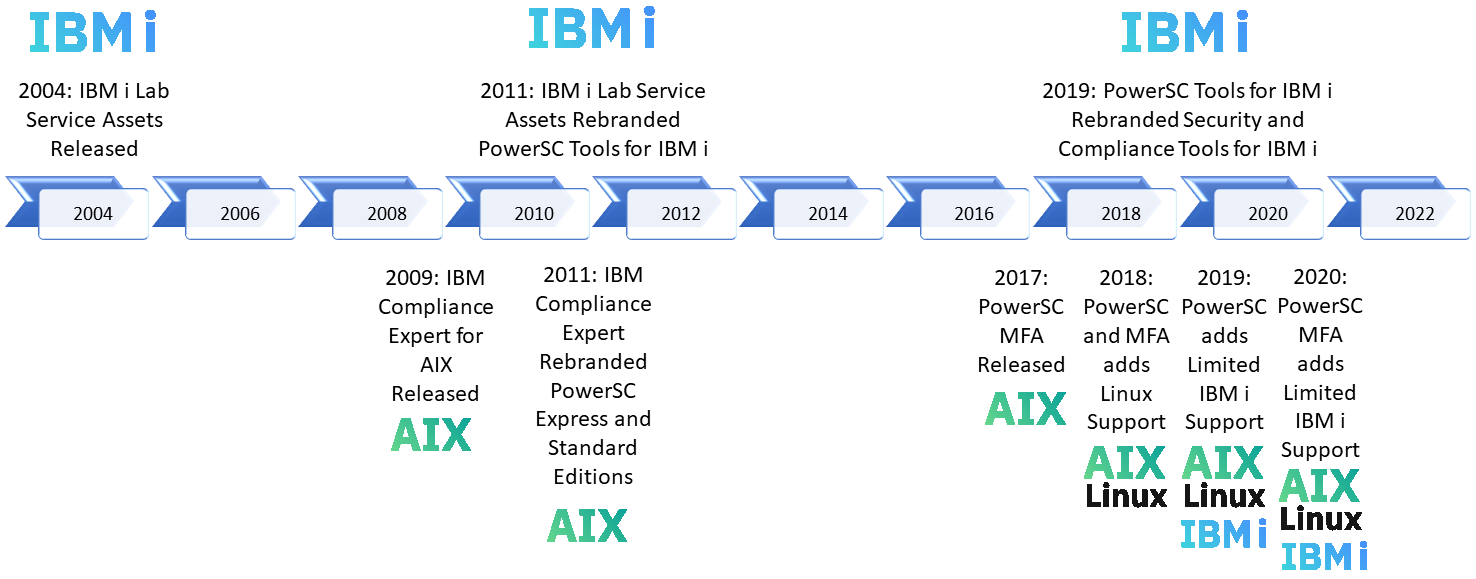
- IBM PowerSC
- Team Members
- Upload Data to our Team
- Statement of Good Security Practices
- IBM i Security Documentation
- IBM i Security Enhancements
- IBM i Security with SQL Services
Learn about Ransomware and IBM i with our Security Thought Leader Robert Andrews!
In order to develop a proper baseline, the IBM i Security Assessment (Video Intro) scans your system for a wide range of security settings and risks. Our review of the core operating system, settings, user profiles, and permissions include:
- Investigate privileged user profiles, command line access, and other significant aspects of the user profiles on the system
- Investigate password practices
- Investigate the use of Group Profiles and Authorization Lists
- Analyze the use of adopted authority and profile swapping
- Examine communications and TCP/IP exposures (Open Ports and Exit Points)
- Examine current system value settings
- Examine current System Service Tools (SST) security settings
- Examine the subsystem descriptions, job descriptions, output queues, and job queues
- Analyze access control for Library system objects
- Analyze access control for IFS directories
- Analyze file shares for ransomware exposure
- Examine current Security PTF levels and determine whether CUSTOMER is within those current levels
- Document the findings and recommendations for securing the system based on findings
- Examine the IBM i auditing and logging practices used by CUSTOMER and provide recommendations for improvement if determined to be insufficient
- Review user, programmer, and admin access to data from application
- Recommend application security design or changes to meet security requirements
- Provide recommendations on proper development security best practices
- Syslog Reporting Manager [Manual] [Video Demo] [Download]
- Single Sign On (SSO) Suite [EPT Manual] [Video Demo] [Download (password required)]
- Certificate Expiration Manager [Manual] [Download]
*Note: All assets have a cost associated with them!! While you are able to download the code and user guides, these assets do not work without a purchased licensed key. To inquire, get a quote, or purchase assets, contact Ron Bibby at ronbibby@us.ibm.com.
IBM i Syslog Reporting Manager (SRM) Licensing Update
As of April 13, 2026, IBM i Syslog Reporting Manager (SRM) will transition from version 2 to version 3.
What’s changing
SRM licensing is moving from a perpetual license with annual SWMA (Software Maintenance) to an annual subscription model. The subscription includes the license, support, and all upgrades.
Existing customers (version 2)
- Your version 2 license is perpetual and will never expire. You may continue using version 2 indefinitely.
- Upon renewal, SWMA contracts will transition to the new subscription model.
- With an active support/subscription contract, you are eligible to upgrade to version 3 at no additional cost. Upgrading is optional.
Important licensing difference:
- Version 2 keys: do not expire
- Version 3 keys: expire at the end of your support/subscription term
There is no option for a non-expiring version 3 license.
If you choose to use version 3:
- Your license key will be valid only for the duration of your subscription
- Each renewal requires applying a new key with an updated expiration date
New customers (version 3)
- All new subscriptions will be for version 3
- There is no upfront license cost—only an annual subscription fee
- The subscription includes product usage, support, and upgrades
- License keys are valid for the subscription term and must be renewed when the subscription is renewed
On January 1, 2026, the IBM i Security Expert Labs team withdrew from marketing (WFM) the following assets:
- Compliance Automation Reporting Tool (CART) [Presentation] [Video Demo] [Download]
- Compliance Automation Reporting Tool (CART) Express [Presentation] [Download]
- Advanced Authentication (formerly Multi Factor Authentication) [Manual] [Video Demo] [Download]
- Network Firewall (Exit Point Security) [Manual] [Video Demo] [Download]
- Privileged Elevation Tool (Fire Call) [Manual] [Video Demo] [Download]
This means that no new purchases of these assets are possible. Any existing software maintenance (SWMA) contracts will be honored until their current end date. Any SWMA contracts expiring by December 31, 2026, will be able to renew for one additional year only. The end of support (EOS) for all these assets will be at the end of the SWMA contract, but no later than December 31, 2027. All support for these assets will end on December 31, 2027. This gives our existing clients two years to determine how they would like to proceed.
For clients looking for a general IBM i Security and Compliance tool, please consider using IBM PowerSC or the tools built into IBM Navigator for i. For prior CART clients and those with large and complex IBM i enterprises, Expert Labs recommends moving to IBM Database Expert Query for i featuring the Compliance Automation Monitor (CAM). For clients looking to implement MFA on IBM i, please move to the no cost integrated MFA features introduced in IBM i 7.6. For specific tactical needs such as exit point application firewalls and privilege elevation tools, please contact one of the many IBM i Security Business Partners (BPs) which have many offerings in this space.
All existing assets will continue to work in their current form on the currently supported operating systems (up to IBM i 7.6). There are no plans to enhance or build versions of these tools that are compatible with future versions of the OS. Licenses purchased are perpetual and will still be valid. Expert Labs does have the ability to generate new license keys for new serial numbers if a client has already purchased these assets. Contact systems-expert-labs@ibm.com if you need a new key for existing licenses.
For a list of the current versions of the Security and Compliance Tools for IBM i, click here.
- Robert Andrews, Principal Security Consultant / STSM, Team Lead, IBM i Security Expert Labs
- Terry Ford, Senior IBM i Security Expert Labs consultant
- Thomas Barlen, European consultant
- Santiago Nunez, Latin America consultant
- Jesus Haro, Latin America consultant
- Jason Tan, Asia Pacific consultant
- Ron Bibby, Contracts and Opportunities
- General IBM Expert Labs Contact