Release Notes
Abstract
This firmware update (v3.3.0) provided by IBM updates QRadar® M5 appliances with microcode security fixes and includes updates for UEFI, IMM2, Dynamic System Analysis, RAID controllers, HDD software, and an Emulex update. This firmware can be used on all QRadar M5s for both 1U or 2U form factor appliances. This firmware update is intended for local USB updates of on-premise M5 xSeries 1U and 2U form factor hardware.
Content
Part 1: About the M5 Firmware 3.3.0 USB/On-premise Update
The M5 firmware update 3.3.0 is intended to update firmware on local QRadar appliances using a USB drive. This update adds new firmware versions and resolves a sizing issue reported in Samsung solid state drives (SSDs): FRU 01GR787, Model number MZILS3T8HMLHV3. See: http://ibm.biz/qradarm5ssd for more info.
The USB drive creation and installation instructions are located on tab 'Part 2. Installing Firmware Updates'. These instructions have been updated to guide customers how to create a bootable USB drive to upgrade their firmware using an IMG file from IBM Fix Central. A remote installation option is available for administrators who prefer to install their M5 firmware updates remotely or for those who do not allow USB keys in their production environments. For more information, see QRadar Firmware 3.3.0 for xSeries M5 Appliances (IMM/ISO for remote installations).
Administrator notes and important information
- Administrators should ensure that all firmware check boxes are selected when the comparison screen displays suggested firmware changes to be installed. We have reports that not all check boxes were selected and administrators had to apply the update again. To prevent additional downtime, administrators should verify all check boxes are selected as defined in the instructions on Tab 2.
- If your appliance is in a HA pair, there are configuration steps required to set the status properly for your primary and secondary high-availability appliances. For more information, see: http://www.ibm.com/support/docview.wss?uid=swg27047121#HA.
- Administrators must enable IMM.Over.LAN on the xSeries appliance BEFORE the firmware update is applied. For information on how to enable this setting, see: http://www.ibm.com/support/docview.wss?uid=swg21982944.
Supported appliances, types, and model information
This firmware update applies to the following IBM Security QRadar M5 appliances, server type, or Machine type models:
| Appliance Name | Server Type | Lenovo Server Machine Type | IBM Machine Type-Model |
|---|---|---|---|
| IBM Security QRadar xx05 G3 | x3550 M5 | MT 8869 | 4412-Q1E |
| IBM Security QRadar Event Collector 1501 G3 | x3550 M5 | MT 8869 | 4412-Q4D |
| IBM Security QRadar Network Insights 1901 | x3550 M5 | MT 8869 | 4412-F4Y |
| IBM Security QRadar xx29 | x3650 M5 | MT 8871 | 4412-Q2A |
| IBM Security QRadar xx48 | x3650 M5 | MT 8871 | 4412-Q3B |
| IBM Security QRadar Incident Forensics | x3650 M5 | MT 8871 | 4412-F1A |
| IBM Security QRadar Network Insights 1920 | x3650 M5 | MT 8871 | 4412-F3F |
| IBM Security QRadar Network Packet Capture | x3650 M5 | MT 8871 | 4412-F2C |
Important file changes and prerequisites in this firmware update
The table below lists the software versions contained within the firmware package. The core change in this release (3.3.0) is to provide new UEFI microcode security updates and IMM2 updates for administrators. Administrators must ensure that their M5 appliance includes the minimum version outlined in the Prerequisite version column, if any pre-requisites are defined.
| Component | Prerequisite version | Firmware version in this update | File name |
|---|---|---|---|
| UEFI/BIOS (1U 8869) | uEFI v1.20 (TCE108i) | tceg38g-2.81 | oem_fw_uefi_tceg38g-2.81_anyos_32-64 |
| UEFI/BIOS (2U 8871) | uEFI v1.20 (TCE108i) | tceg38g-2.81 | oem_fw_uefi_tceg38g-2.81_anyos_32-64 |
| IMM2 | tcoe26o (version 3.75) | tcoe46f-5.11 | oem_fw_imm2_tcoe46f-5.11_anyos_noarch |
| DSA | None | dsaob2s-10.4 | oem_fw_dsa_dsaob2s-10.4_anyos_anycpu |
| Emulex* | None | 2.10x6-9 | elx-lnvgy_fw_fc_18a-2.10x6-9_linux_x86-64 Note: No version change from the M5 v3.2.1 firmware release. |
| RAID Controller M1215 | None | 1200-24.21.0-0067-2 | lnvgy_fw_sraidmr_1200-24.21.0-0067-2_linux_x86-64 |
| RAID Controller M5210 | None | 5200-24.21.0-0067-2 | lnvgy_fw_sraidmr_5200-24.21.0-0067-2_linux_x86-64 |
| HDD Update | None | 1.27.09 | lnvgy_fw_hdd_sas-1.27.09_linux_x86-64 |
Security issues resolved in this firmware update
The table below lists the software versions contained within the firmware package and the applicable CVEs addressed in this firmware release.
| Component | File name | CVEs resolved in this package |
|---|---|---|
| UEFI/BIOS (1U 8869) | oem_fw_uefi_tceg38g-2.81_anyos_32-64 | None |
| UEFI/BIOS (2U 8871) | oem_fw_uefi_tceg38g-2.81_anyos_32-64 | None |
| IMM2 | oem_fw_imm2_tcoe46f-5.11_anyos_noarch | CVE-2018-0737, CVE-2018-1000120, CVE-2018-1000121, CVE-2018-1000122, CVE-2018-1000301, CVE-2018-14404, CVE-2018-15473 |
| DSA | oem_fw_dsa_dsaob2s-10.4_anyos_anycpu | None |
| Emulex* | elx-lnvgy_fw_fc_18a-2.10x6-9_linux_x86-64 | None |
| RAID Controller M1215 | lnvgy_fw_sraidmr_1200-24.21.0-0067-2_linux_x86-64 | None |
| RAID Controller M5210 | lnvgy_fw_sraidmr_5200-24.21.0-0067-2_linux_x86-64 | None |
| HDD Update | lnvgy_fw_hdd_sas-1.27.09_linux_x86-64 | None |
| Other Security Fixes | None | Security vulnerabilities resolved in open source packages where there is no IMM exposure: CVE-2017-17833, CVE-2018-0732, CVE-2008-1483, CVE-2016-10012, CVE-2016-10708, CVE-2017-15906 |
NOTE: Administrators can use any text editor to review a detailed change list for firmware update v3.3.0. Click the .txt file and open the document in any text editor program.
QRadar_All_M5_1U_MT8869_x3550_2U_MT8871_x3650_3_3_0_0.txt
IMPORTANT: Administrators must enable IMM.Over.LAN on the xSeries appliance BEFORE the firmware update is applied. For information on how to enable this setting, see: http://www.ibm.com/support/docview.wss?uid=swg21982944.
Creating your USB flash drive for the firmware update requires a Windows host and the administrator or USB drive must be on-site with the appliance. The firmware update can take up to 60 minutes complete per appliance and the administrator will be required to reboot the appliance after the firmware install completes. The firmware upgrade procedures should only be done during a change window or during maintenance time for your QRadar appliances.
You must have access to the following items:
- An 8 GB or larger USB flash drive
- A desktop or notebook system running one the following operating systems:
- Windows 10
- Windows 7
- Windows 2008R2
- Windows 2008
- Windows Vista
- Windows XP
Creating the bootable USB drive
- Download the M5 v3.3.0 firmware IMG file from IBM Fix Central: http://www.ibm.com/support/fixcentral/swg/quickorder?parent=IBM%20Security&product=ibm/Other+software/IBM+Security+QRadar+SIEM&release=7.3.0&platform=All&function=fixId&fixids=7.3.1-QRADAR-FIRMWARE-M5_1U_USB-QRadar-QNI-PCAP-QIF-3.3.0&includeSupersedes=0&source=fc
- Download the Rufus tool from Rufus Downloads (http://rufus.akeo.ie/downloads/).
- Insert the USB flash drive into a USB port on your Windows laptop or workstation.
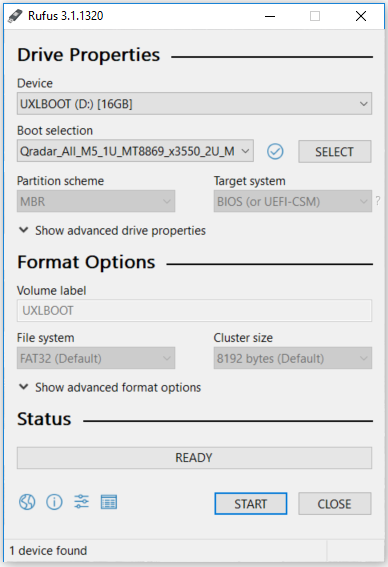
- Open Rufus and configure the properties.
Parameter Value Device Select your USB drive Boot Selection Select Qradar_All_M5_1U_MT8869_x3550_2U_MT8871_x3650_3_3_0.img Partition scheme MBR (Default) Target system BIOS (or UEFT-CSM) (Default) File system FAT32 (Default) Cluster size 4096 bytes (Default) - Click Start. The image is loaded on the USB drive.
- After the installation finishes, safely eject the USB flash drive from your computer.
Installing the firmware update
This procedure requires you to reboot your QRadar appliance after the firmware update is installed. Administrators should expect a data outage while firmware updates are applied.
- Insert the USB drive in to the M5 QRadar appliance.
- Reboot the system to start the software installation process.
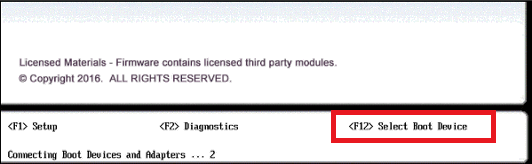
- As the appliance is rebooting, press the F12 key to select a boot device.
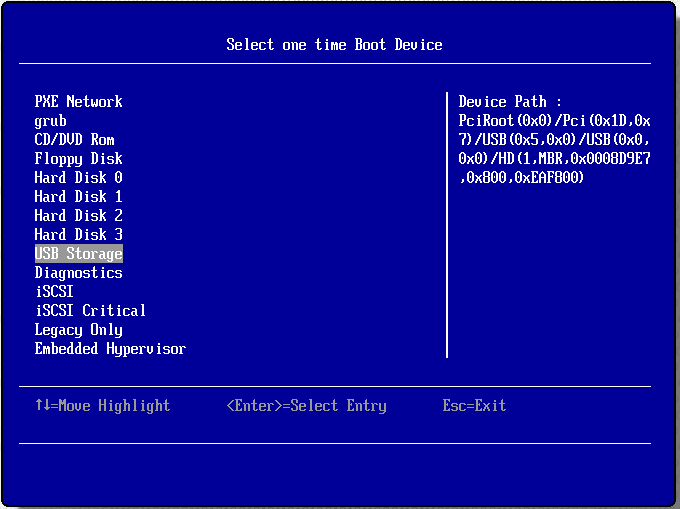
- Select the bootable firmware image, for example, USB Storage and Press Enter.
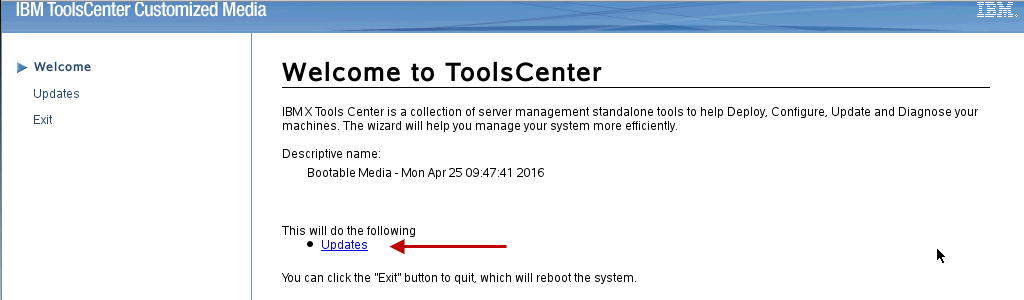
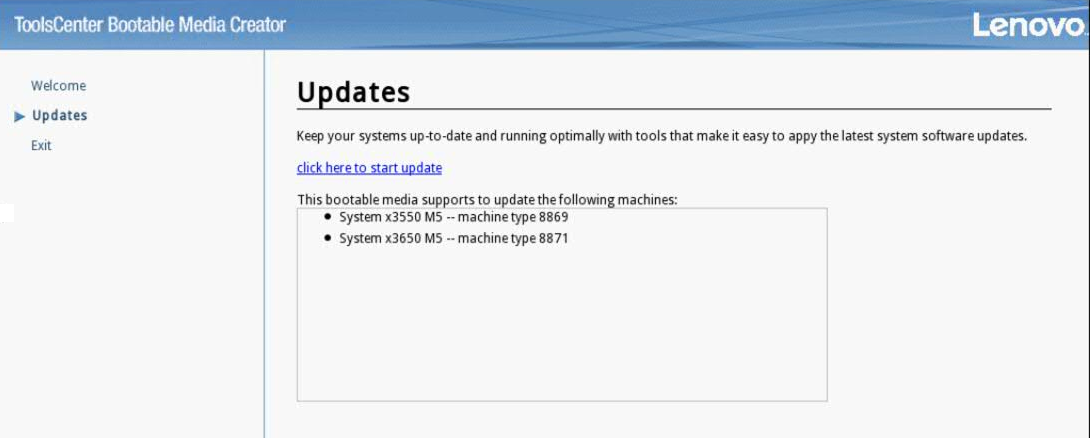
- The IBM ToolsCenter Welcome page is displayed.
- When prompted, select the Updates option.
- Verify that the bootable media shows the correct machine type for the appliance.
Hardware Number Server Type x3550 M5
x3650 M5Server Machine Type MT 8869
MT 8871 - To start the update, select Click here to start update.
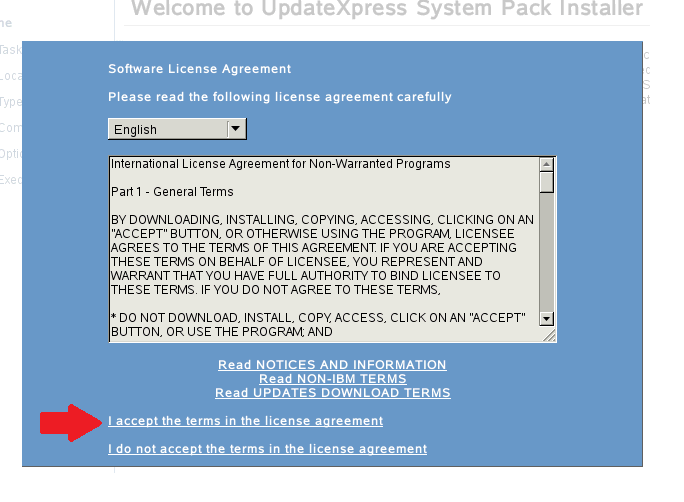
- Select your language and click I accept the terms in the license agreement to continue.
- The IBM UpdateXpress System Pack Installer compares the current package with the installed firmware

- **IMPORTANT:** Review the list of updates and confirm that all Suggested updates are included. It has been reported that some suggested updates are not selected by default. Administrators should verify check boxes are selected to prevent additional downtime.
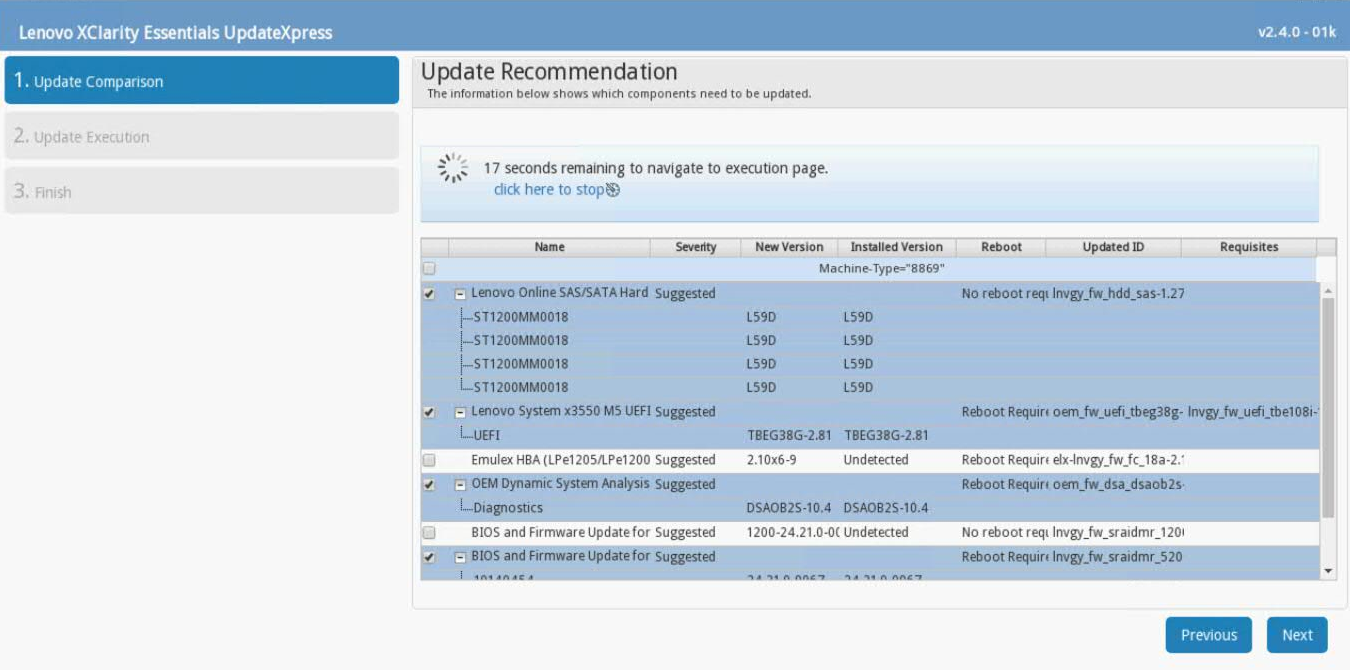
- To apply the firmware updates, click Next on the Update Options page.
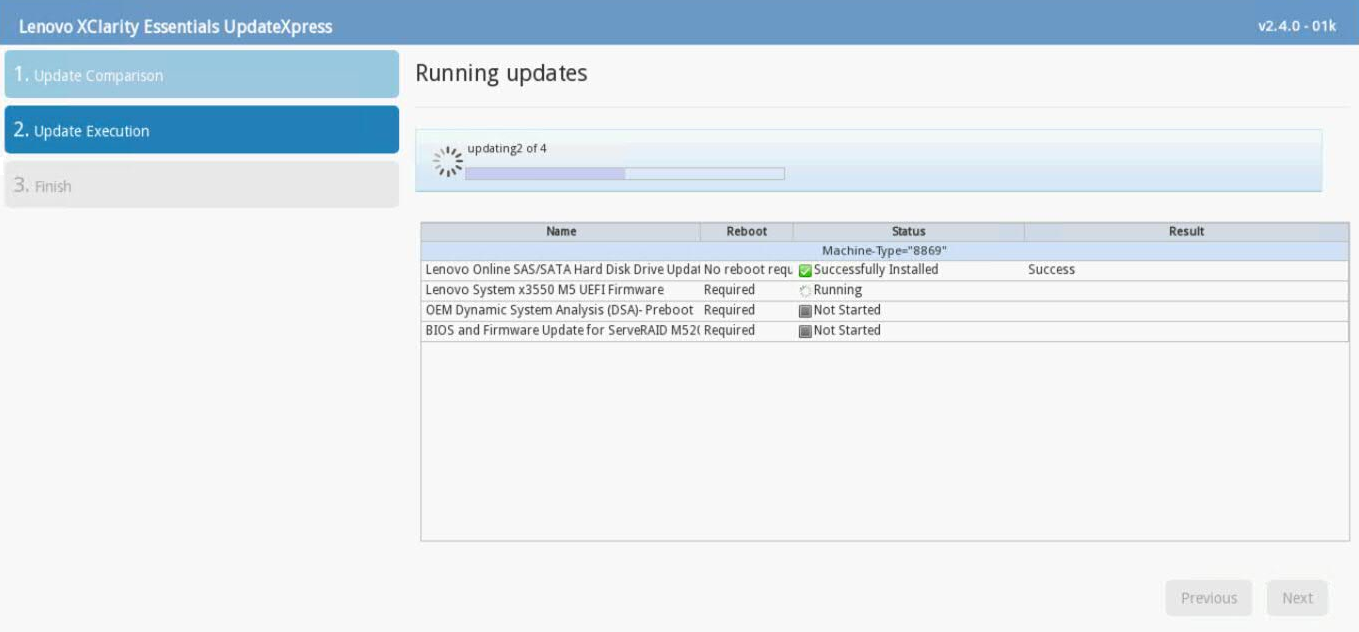
- Verify that all the firmware updates are applied, and click Next to complete the update.
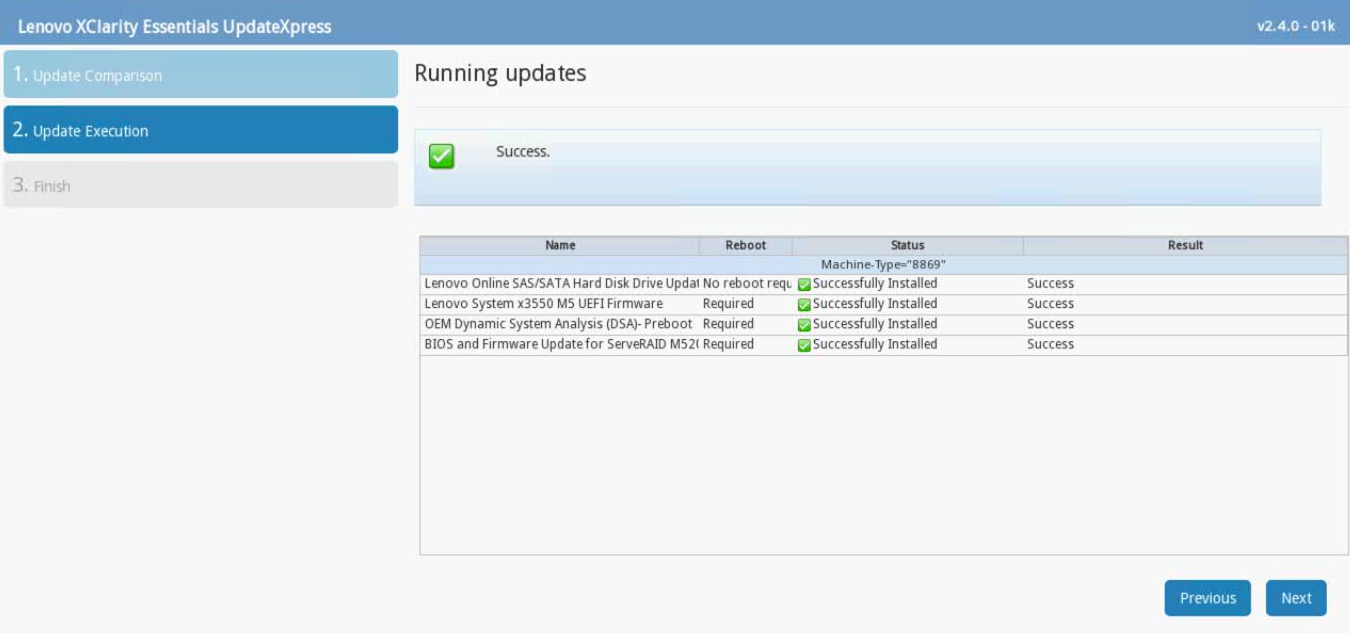
- After the update is complete, click Save Log to save the installation log to the USB flash drive. This file can be provided to support in case any issues occurred during the update.
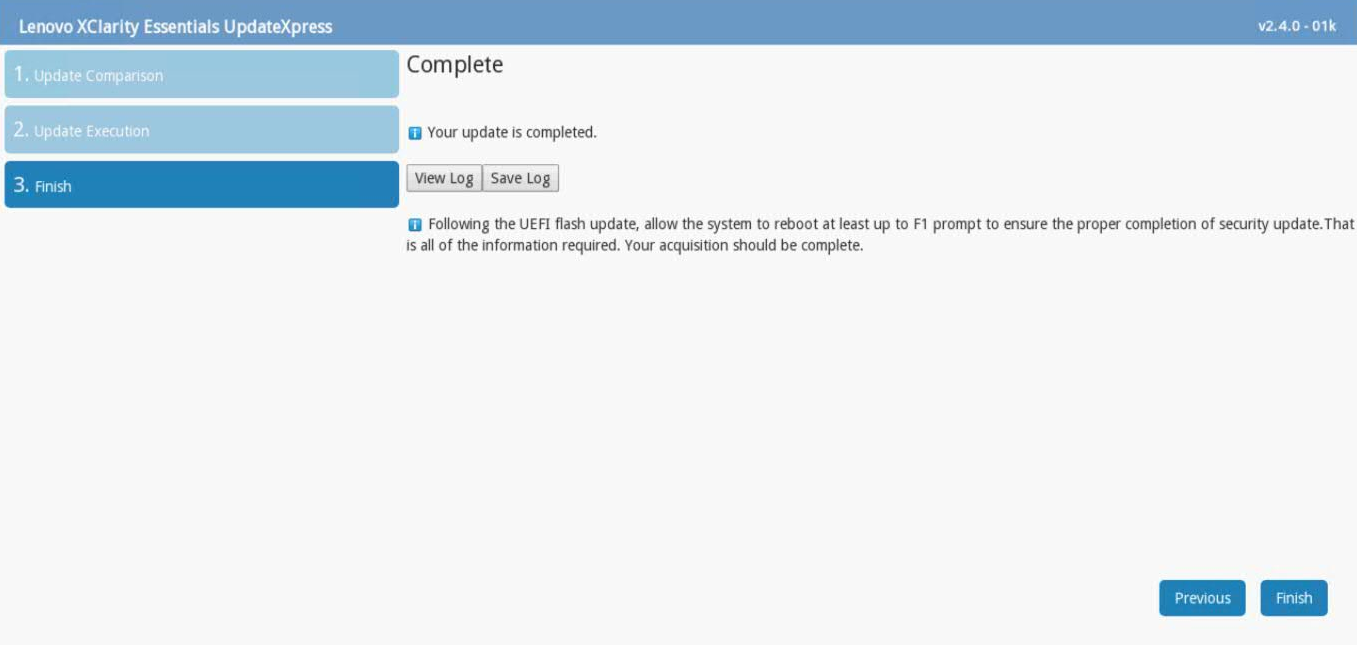
- Select the USB flash drive and click OK.
- After the log is saved, click Finish to reboot the appliance.
Results
Wait for the appliance to reboot. After any UEFI update, administrators should allow the appliance to boot past the F1 prompt to ensures that all updates are installed.
Troubleshooting
If you have any issues with the appliance booting or with firmware update problems, you can open a case with QRadar Support. If you have issues with the appliance booting after you update firmware, attach your update collect preboot DSA logs from the QRadar appliance.
The firmware installer might issue an Emulex error to administrators that can be ignored. Not all QRadar M5 appliances ship with an Emulex card. The firmware update contains software to attempt to update the Emulex drivers; however, if the appliance does not include an Emulex, an installation error will be displayed, "Install did not succeed".

Was this topic helpful?
Document Information
Modified date:
31 March 2020
UID
ibm10879625