Question & Answer
Question
How can I configure Single Sign-on using the IBM Navigator for i GUI?
Answer
NOTE: If you would like to configure Single Sign-on using the Heritage Navigator for i, please refer to the following documentation:
How to configure EIM and NAS using IBM Heritage Navigator for i
Configuring Single Sign-On using IBM Navigator for i
Prerequisites
It is recommended to go through the Single Sign-on Configuration Planning Worksheets prior to configuring Single Sign-on. The worksheets can be found here: Single Sign-on Configuration Planning Worksheets
The IBM Tivoli Directory Server (LDAP) must be active and have a basic working configuration. If a cleanup and configure of LDAP is needed, refer to Complete LDAP / Directory Server Cleanup and Reconfigure
The HTTP *Admin server must be active and at the latest HTTP group PTF level (see the following for the latest group levels available):
IBM i Group PTFs with level
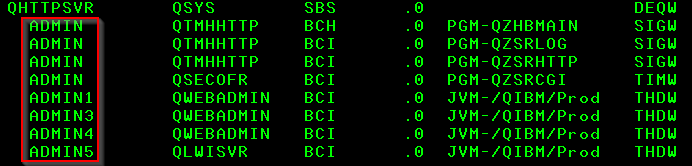
To access the IBM Navigator for i page the HTTP server ADMIN must be active in the QHTTPSVR subsystem as seen below. If it is not active, use the following command:
STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN)
This may take anywhere from 5 minutes to 1/2 hour + (depending on system size/resources) to become fully active.**
Access the IBM Navigator for i page
If the Admin jobs are active, use one of the following URLs and replace <IBMiFQDN> with your IBM i Fully Qualified Domain Name (FQDN - host.domain from CFGTCP Option 12):
http://<IBMiFQDN>:2002/Navigator
OR
https://<IBMiFQDN>:2003/Navigator
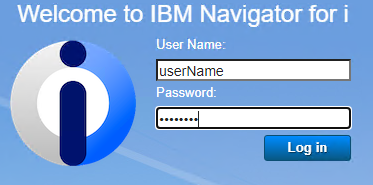
You should be prompted for your user ID and password. This is the same user ID and password you use to log into the IBM i system.
- Configure Network Authentication Service (NAS)
We recommend configuring NAS prior to configuring EIM. This is due to the fact that the majority of problems seen with initial configuration is due to improper NAS configuration and/or DNS resolution issues. For this reason it is highly recommended that you first go through the NAS configuration and test it prior to moving on to the Enterprise Identity Mapping (EIM) setup.Host Name Resolution - The #1 most common problem with new SSO configurations
Take note of the following two crucial elements that will help you get a successful NAS configuration:
- Have the IBM i system's fully qualified domain name (FQDN) as the first name in the list for the IP address it is associated with in the local host table (LHT).

- Test DNS lookups for the IBM i using both the name and the IP. Note that it is recommended the same DNS server is used by the client PC and the IBM i. You can check what DNS server you are using on the IBM i by typing CHGTCPDMN <F4> and page down to see the Domain Name Servers. The top one in the list is the primary one used.
To test the DNS lookups you can use the NSLOOKUP command from your PC's command prompt. You can also do this on the IBM i but you need 5770SS1 option 31 (Domain name server) installed for the NSLOOKUP command to work. Note the commands used in the image below and the results.

In the above screenshot the things to note are the IP address returned from the first lookup of the name used (rch730a.rchland.ibm.com) and the name returned when using "set type=ptr" to change the lookup to a "Reverse Lookup". In this case the system name returned is the same fully qualified domain name that was entered above. This is a successful test. If the name returned by the PTR lookup was different than the name you typed in for the "A" record lookup (meaning it comes back with either JUST the short name or a different name entirely, or no name at all), an adjustment would need to be made to the DNS server to fix the record.
**Refer to your planning worksheet details for what information to fill in the fields as you go through the wizard.**
Step 1 - Open Network Authentication Services from the Navigator for iEnsure the managed node you are connecting to in Navigator is configured with a "Node Hostname" pointing to the IBM i FQDN (host.domain) configured under CFGTCP Option 12. The "Node Hostname" value cannot be set to the IP address of the IBM i. This will affect the service principal values created by the wizard.Right-click on the node and select "Edit Node Information". Ensure the "Node Hostname" field is configured to the value of your IBM i FQDN (host.domain) configured in CFGTCP Option 12.If the "Node Hostname" field is not correct, you will need to add a new node.
Ensure the "Node Hostname" field is configured to the value of your IBM i FQDN (host.domain) configured in CFGTCP Option 12.If the "Node Hostname" field is not correct, you will need to add a new node. On the Add New Node pop-up, fill in the Node Hostname, User Name and Password
On the Add New Node pop-up, fill in the Node Hostname, User Name and Password Click the OK button to add the new node.Take note that Node Display Name not the Node Hostname will be in the node tile. Now click on Manage inside the node tile to manage your server
Click the OK button to add the new node.Take note that Node Display Name not the Node Hostname will be in the node tile. Now click on Manage inside the node tile to manage your server Now, hover over the Security icon on the left menu, then click 'Network Authentication Service' > 'Configuration Wizard'.
Now, hover over the Security icon on the left menu, then click 'Network Authentication Service' > 'Configuration Wizard'.
Step 2 - Specify realm informationThe Default realm is typically the Microsoft Windows domain that the users log in to from their PC. If you are using a Windows server (any version) as your primary domain controller, leave the box checked for "Microsoft Active Directory is used for Kerberos authentication". In the image below, "711.LAB" is used for our local domain example.
Step 3 - Specify the fully qualified domain name of your KDCThe KDC (or Key Distribution Center) is typically the primary Windows server that has Active Directory configured on it. The Fully Qualified Domain Name refers to the server's full name, which is the host name...or system name, with the domain name appended to it. The default Kerberos port is 88 which should not be changed unless your network administrator has specifically changed this on the KDC. This example uses the server's host name of ctawinsvr.711.lab and the domain of rchland.ibm.com is appended to it to make the fully qualified domain name (or FQDN).


Step 4 - Specify Password Server InformationThe default values can be kept here. The explanation of the password server is at the top of this window. Click Next to continue.Step 5 - Select the keytab entries to be created By default, all boxes are checked. Each one will create service principal entries for the respective service. The service used for all 5250 and telnet emulation sessions is the top one - IBM i Kerberos Authentication.You will need to create a password that will be set for all service principals. These passwords will ONLY be used to encrypt/decrypt the tickets by the KDC and the IBM i. Be sure that the password used falls within the password policies in place for your KDC (typically the Microsoft AD server).*NOTE* Use caution when configuring NetServer for SSO. If the principal is added to the Active Directory server (one of the last steps of NAS configuration) and you have not yet created EIM Identifiers and Associations for users, you may experience a loss of NetServer service (mapped drives to the i).
By default, all boxes are checked. Each one will create service principal entries for the respective service. The service used for all 5250 and telnet emulation sessions is the top one - IBM i Kerberos Authentication.You will need to create a password that will be set for all service principals. These passwords will ONLY be used to encrypt/decrypt the tickets by the KDC and the IBM i. Be sure that the password used falls within the password policies in place for your KDC (typically the Microsoft AD server).*NOTE* Use caution when configuring NetServer for SSO. If the principal is added to the Active Directory server (one of the last steps of NAS configuration) and you have not yet created EIM Identifiers and Associations for users, you may experience a loss of NetServer service (mapped drives to the i). Step 6 - Batch FileThis next screen gives you the option of having the wizard generate a batch file which must be sent to, and run on the Microsoft Windows Active Directory server (only).Note that the default location and name of the batch file stored as /QIBM/UserData/OS400/Navigator/config/NASConfig_<node display name>.bat(The name will change depending on your node display name as you will see the one here is called NASConfig_rch750b.bat because my example system's node display name is rch750b).If you do not want the passwords included in the batch file, remove the check from the respective check box. Be aware though that you will be prompted to manually enter the password for each service principal while the batch file runs on the AD server. Any mistakes will cause failures with the Single Sign-on connections. We recommend checking the box next to the option "Set the AD service principal passwords to never expire". If a service principal password expires, SSO connections that use that principal will fail to connect. If this happens, the password must be changed/renewed not only on the AD entry, but in the NAS keytab list as well.
Step 6 - Batch FileThis next screen gives you the option of having the wizard generate a batch file which must be sent to, and run on the Microsoft Windows Active Directory server (only).Note that the default location and name of the batch file stored as /QIBM/UserData/OS400/Navigator/config/NASConfig_<node display name>.bat(The name will change depending on your node display name as you will see the one here is called NASConfig_rch750b.bat because my example system's node display name is rch750b).If you do not want the passwords included in the batch file, remove the check from the respective check box. Be aware though that you will be prompted to manually enter the password for each service principal while the batch file runs on the AD server. Any mistakes will cause failures with the Single Sign-on connections. We recommend checking the box next to the option "Set the AD service principal passwords to never expire". If a service principal password expires, SSO connections that use that principal will fail to connect. If this happens, the password must be changed/renewed not only on the AD entry, but in the NAS keytab list as well. What does this batch file do?The batch file is created to make it easy for you to add the required Active Directory user entries. It takes a few seconds to run, adds all of the required service principals to Active Directory, and it is in plain text so you can edit the file to see what is in it (no hidden commands or functions). Many Windows administrators prefer to add the entries themselves which is ok, as long as it is done correctly. When incorrectly added, NAS (and therefore Single Signon) will fail to work. Here is an excerpt of what is in the batch file when generating a principal for krbsvr400.
What does this batch file do?The batch file is created to make it easy for you to add the required Active Directory user entries. It takes a few seconds to run, adds all of the required service principals to Active Directory, and it is in plain text so you can edit the file to see what is in it (no hidden commands or functions). Many Windows administrators prefer to add the entries themselves which is ok, as long as it is done correctly. When incorrectly added, NAS (and therefore Single Signon) will fail to work. Here is an excerpt of what is in the batch file when generating a principal for krbsvr400.DSADD user "cn=rch750b_1_krbsvr400,cn=users,dc=711,dc=LAB" -pwd Passw0rd -display rch750b_1_krbsvr400 -pwdneverexpires yes -desc "IBM i Kerberos services on system rch750b"
KTPASS -MAPUSER rch750b_1_krbsvr400 -PRINC krbsvr400/RCH750B.711.LAB@711.LAB -PASS Passw0rd -mapop set -crypto All -ptype KRB5_NT_PRINCIPAL*Note* The password PasswOrd is included in this batch file example in plain text. If you unchecked the box "Include password in the batch file" from the previous screen capture above, the password would not show in this batch file.
Once the batch file is run on the AD server (or if the Windows administrator correctly added the account to AD) it should look similar to this:In this image you can see the default naming convention when the batch file is run on the Active Directory server. The default location that the batch file creates these accounts is in the domain Users folder shown on the right. The default name of the accounts will have the system name followed by a number, then the service principal prefix. 
This is an image of the properties of the user account. Note that we are concerned with the details of the Account tab. The User logon name should look like the example to the right, but it should show your own system name and domain. Note that the checkbox for "Password never expires" is checked. If the box is not checked, the password will expire after the number of days dictated by the Windows Password Policy. If this happens, all users connected via Kerberos authentication will fail to connect.  Under the Account options section, check the box(es) for the AES 256 and/or 128-bit encryption types. Uncheck the box for DES encryption.Click the Apply button to confirm the change.
Under the Account options section, check the box(es) for the AES 256 and/or 128-bit encryption types. Uncheck the box for DES encryption.Click the Apply button to confirm the change.
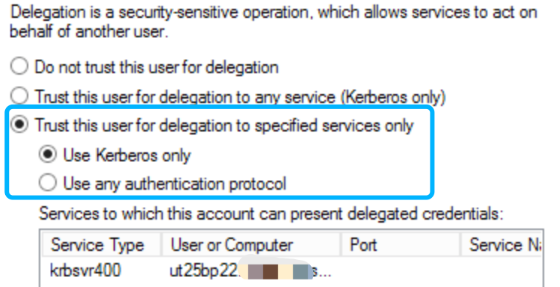
 This is an image of the Delegation tab of the same user account for krbsvr400. Delegation is not necessarily required for getting SSO to work for Telnet/5250 sessions, but it is required for a number of other applications to function with SSO, including FTP, QNTC, HTTP, and several others. For this reason, it is recommended the options be set similar to what is shown here. Windows administrators may be able to customize this further to their own requirements if necessary.More and more customers report to have a security remark on the AD/KDC server when allowing the trust for delegation to any service. If that is the case those customer can choose to set the delegation to the specified services only, as in the screen shot, where the principal is delegating only using Kerberos and the services are specified.It remains however an AD setting and it is the Administrator of the AD that is responsible for this setting.
This is an image of the Delegation tab of the same user account for krbsvr400. Delegation is not necessarily required for getting SSO to work for Telnet/5250 sessions, but it is required for a number of other applications to function with SSO, including FTP, QNTC, HTTP, and several others. For this reason, it is recommended the options be set similar to what is shown here. Windows administrators may be able to customize this further to their own requirements if necessary.More and more customers report to have a security remark on the AD/KDC server when allowing the trust for delegation to any service. If that is the case those customer can choose to set the delegation to the specified services only, as in the screen shot, where the principal is delegating only using Kerberos and the services are specified.It remains however an AD setting and it is the Administrator of the AD that is responsible for this setting.
 Step 7 - Test the NAS configuration
Step 7 - Test the NAS configuration- Now that the NAS configuration is complete and the batch file has been run on the AD server (or the entries were created manually), it is time to test the configuration. Before we do this however, to avoid one of the common errors we see, we will want to check that the user profile running the steps below has a /home/<user> directory in the IFS. If not, you can use the command mkdir /home/<user profile name>. This MUST exist or you will get an error when running the steps below.
- Once that is done, use these steps to test NAS:
1. Open QSHELL on your IBM i emulation session using the command QSH <enter>
2. Type keytab list and hit enter
3. Scroll back up until you find the krbsvr400/<system.domain> entry similar to the screen capture below and then copy that entry name
4. Type kinit -k and paste in the krbsvr400 entry after it, then hit enter.
- Once that is done, use these steps to test NAS:

- The blue arrow in the image above points to the $ prompt. If you get this back after issuing the kinit -k command (as shown in the image) then you have a successful test.
Congratulations! Now it's time to configure EIM.
- Have the IBM i system's fully qualified domain name (FQDN) as the first name in the list for the IP address it is associated with in the local host table (LHT).
- IBM Tivoli Directory Server (LDAP) Setup
The IBM Tivoli Directory Server (LDAP server) must be active and have a basic configuration. All EIM data is stored within LDAP, however it will not affect any existing LDAP configurations. If LDAP is not functioning and it is NOT currently in use, you can use the instructions on the Complete LDAP / Directory Server Cleanup and Reconfigure page to start with a fresh LDAP setup.
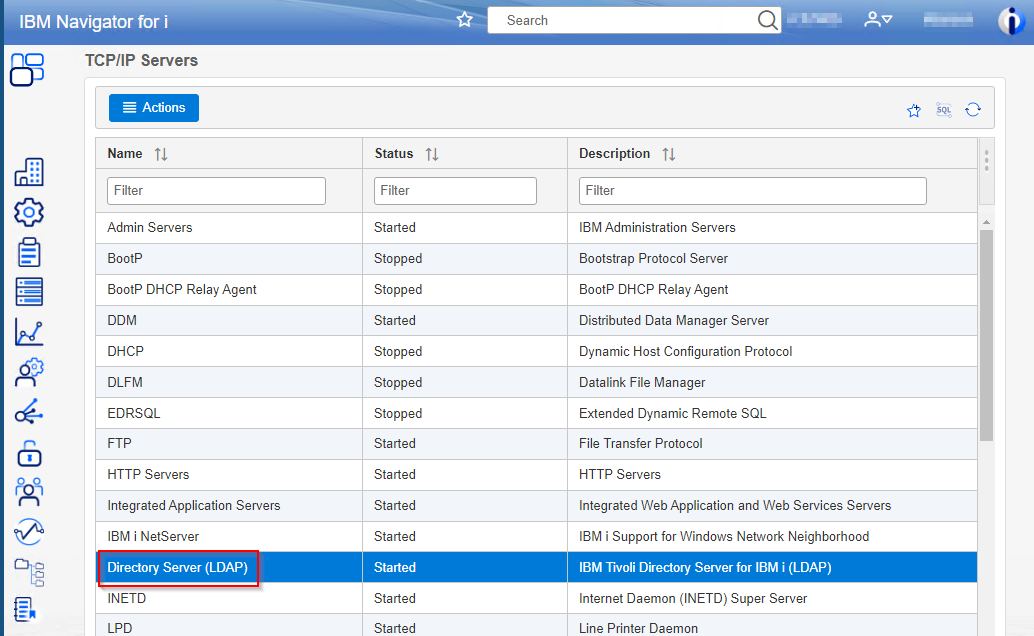
Once LDAP is configured or if it is already configured, you will need to know the password for cn=administrator. This is the default LDAP administrator account. You can set this in the properties for the IBM Tivoli Directory Server by hovering over the Network icon , then click Network > Servers > TCP/IP Servers.
, then click Network > Servers > TCP/IP Servers.- 1. Right-click IBM Tivoli Directory Server for IBM i and click on "Properties"
- 2. On the General tab, click on the "Password" button next to Administrator name: cn=Administrator
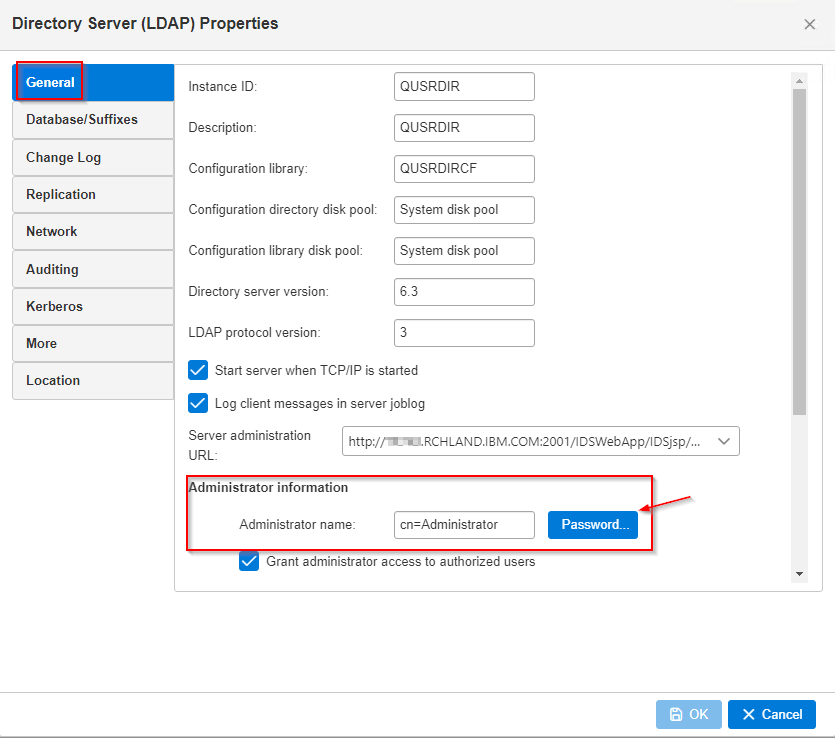
- 3. Set the desired password for the LDAP administrator and click OK.
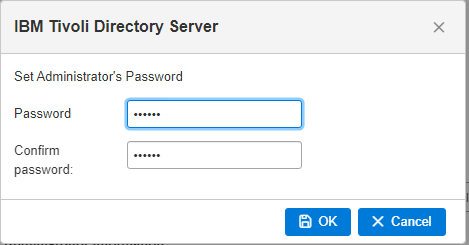 Then click OK again on the LDAP properties page. This will set the LDAP administrator password which will be used in the EIM configuration wizard and for future editing of the EIM entries.
Then click OK again on the LDAP properties page. This will set the LDAP administrator password which will be used in the EIM configuration wizard and for future editing of the EIM entries.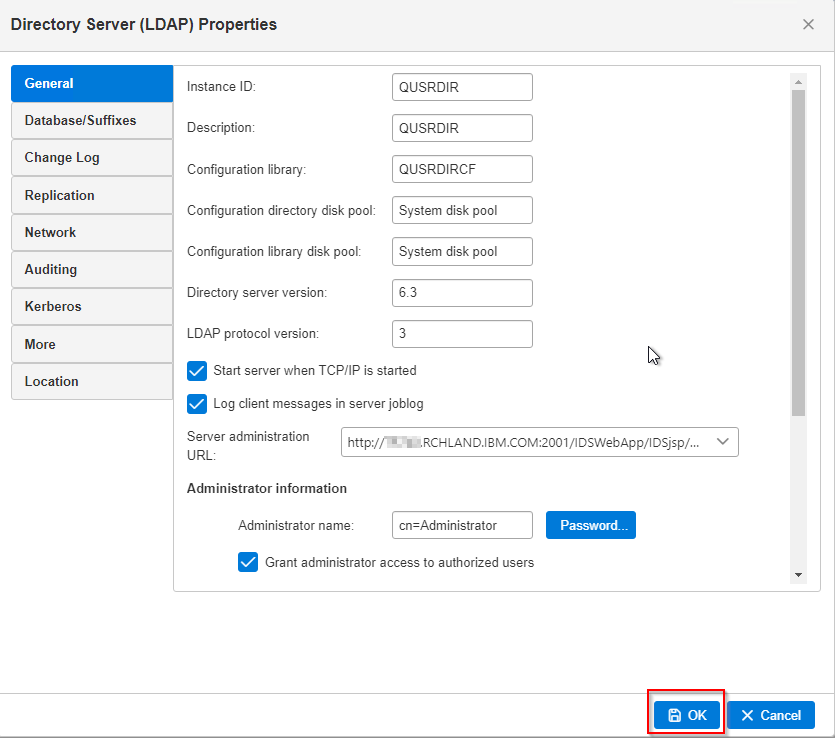
- Once the password is set, you can start the EIM Configuration Wizard.
- 1. Right-click IBM Tivoli Directory Server for IBM i and click on "Properties"
- Configure Enterprise Identity Mapping
Step 1 - Open Enterprise Identity Mapping from the Navigator for i window and start the configuration wizard- Hover over the Security icon, then click Click on Enterprise Identity Mapping > Setup Wizard to start the wizard.

Step 2 - Take the default options of "Create and join a new domain" and "On the local directory server"
*NOTE* The "New domain" referred to here is an EIM domain, not a Windows domain. It is created within LDAP and is separate from any other parts of LDAP or domains. It will not interfere with any network domains.- The Directory Server it refers to is the local LDAP server on the i. As stated previously, EIM data is stored in LDAP on the i. Click Next to continue.

Step 3 - Do not configure Network Authentication Service- NAS was configured in the first part of this document. You can select "No" and click Next to continue.

Step 4 - Specify User For Connection- The configuration wizard needs to connect to LDAP with an authorized user/administrator. The default is the LDAP administrator distinguished name of cn=Administrator. You will need to know the password for cn=administrator which you should have set just prior to these steps (If not, refer to the 3 steps under the title: "Before configuring EIM" earlier in this document).
- Enter the password, then click on "Next" to continue.

Step 5 - Specify the EIM Domain Name and Parent Distinguished Name- The default domain name is simply EIM. You can change this to something else if you prefer but it is not required.
- You do not have to specify a Parent DN for the EIM data. By default, the EIM Wizard will create the EIM data in its own subdirectory. This option is only recommended for those who are familiar with LDAP administration. We recommend keeping this option at its default value of "No".

Step 6 - Registry Information
The Registry Information should already be filled in based on values entered in the NAS configuration. Leave the default values (which should have your IBM i fully qualified name as the Local IBM i and the domain name for your Windows domain server). Click Next to continue.
 Step 7 - Specify EIM System User
Step 7 - Specify EIM System User- The operating system connects to the domain controller as this user when performing EIM functions. The default value is cn=Administrator which is fine. Specify the password for the cn=Administrator and then click Next to continue.

Step 8 - Summary page- The next screen is just a summary of the settings you selected through the wizard. Click on Finish and wait for the wizard to complete. Once it is done you will need to add Identifiers and their associations.

- Create Identifiers and Associations in EIM
What are Identifiers?- In a normal setup, an Identifier basically represents a person. An Identifier must be created, and associations added to that Identifier before that individual can use the EIM infrastructure. All EIM Identifiers must be unique, so two individuals with the same first and last name should have a way to distinguish which Identifier is for which individual. For example; two people named John Smith can be defined by their first name, middle initial, and last name which results in different Identifiers - John R. Smith and John J. Smith.
- Associations are the relationships between an EIM Identifier and that person's profiles on individual systems. This allows EIM to map individuals to their user profiles on multiple systems, even if the user profile is different on each system. Using our example of John Smith; one system may have a user profile of JSMITH, while another system has him as JOHNS. With correct associations, John Smith is logged on as the correct user in either system automatically.
Step 1 - Open the EIM DomainHover over the Security Icon, then click on Enterprise Identity Mapping > Domain Management. This will prompt you for your cn=Administrator password to connect to LDAP. Supply the password, then click "OK".
This will prompt you for your cn=Administrator password to connect to LDAP. Supply the password, then click "OK". This should show you your EIM domain in the right frame. Right-click the domain and click on "Open".
This should show you your EIM domain in the right frame. Right-click the domain and click on "Open".
Step 2 - Create an Identifier
Right mouse button click then click on Open Click on the 'Actions' button and click on "New Identifier".
Click on the 'Actions' button and click on "New Identifier".
Step 3 - Enter the name of the Identifier and Add Associations
Add the Identifier name (It must be unique, meaning you cannot have another Identifier with the same name), then click the 'Actions' button and click 'Add'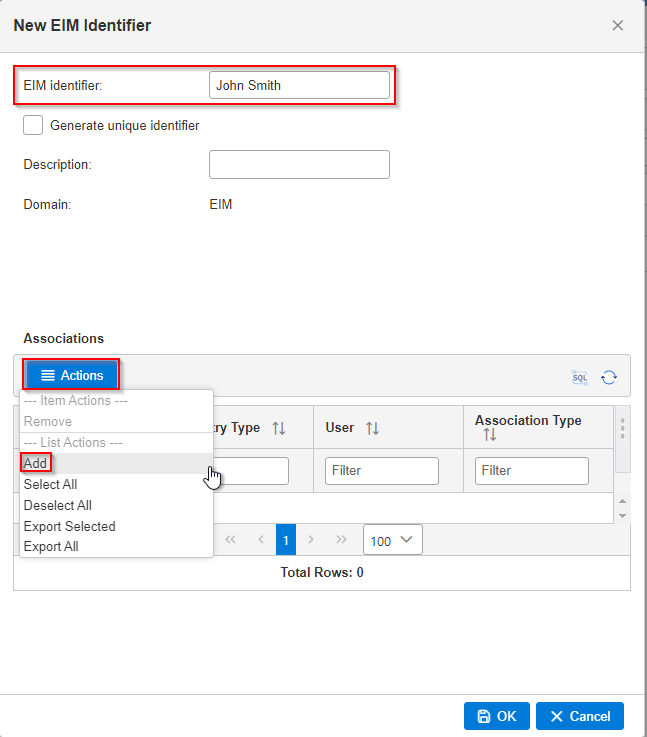
- The "Add Association" window allows you to select a Registry (which represents your systems), add a user name, and select an Association type.
At this point you will only have 2 options for Registries; the local IBM i system name, and the Windows domain (which represents your AD server).

- With "Registry" set to your IBM i system name, add the user profile name you want to have associated with this account. In this case, John Smith will be JSMITH.
- When the Registry is set to your IBM i server name, the Association Type should be set to "Target" because this system will receive Kerberos tickets, it does not generate them.
- Click OK.
**Every Identifier must have, at a minimum, one Target association and one Source association. A Source association is where the Kerberos tickets are created. This, in most cases, is a Windows server. A Target association is a system that will be receiving the tickets.**4. Since we just created our Target association in the previous window, you will now need to create the Source association. To do this, click on the 'Actions' button again and then click "Add" again.
5. Next click the "Browse" button next to "Registry" and select the registry with the type of "Kerberos". This usually will be your Windows domain name and Click OK.
 6. Add the user profile that this person logs into the Windows domain with (their network user ID when signing into their PC).
6. Add the user profile that this person logs into the Windows domain with (their network user ID when signing into their PC).7. Change the Association type to "Source" and click OK.

8. You now have a Source and a Target association for this user. Click OK from the Associations page and click OK when you see message that the user was created.

Congratulations! EIM is now configured and has a user who is ready to test Single Sign-On!
- Enabling Kerberos Authentication
Enabling Kerberos Authentication For Access Client Solutions (ACS) and 5250 Emulation
To enable Kerberos authentication for one or more systems through ACS, you can either specify it on the 5250 emulator or you can set it from the ACS System Configurations window.Step 1 - Open ACS and click on System Configurations Step 2 - Select the system that Kerberos was configured for and click Edit.
Step 2 - Select the system that Kerberos was configured for and click Edit.
Step 3 - Click the "Connection" tab, select "Use kerberos authentication...", and click "Apply" After applying the changes, you should be able to log in without using passwords. It is possible that you may need to request new credentials from the Windows server.This can be done by logging off from your PC and then logging back into the network or possibly by using the KLIST PURGE command from a Windows command prompt.
After applying the changes, you should be able to log in without using passwords. It is possible that you may need to request new credentials from the Windows server.This can be done by logging off from your PC and then logging back into the network or possibly by using the KLIST PURGE command from a Windows command prompt.If you are still prompted to log into the system after enabling Kerberos, check WRKSYSVAL QRMTSIGN from an IBM i session on your system and make sure it is set to *VERIFY instead of *FRCSIGNON.

Was this topic helpful?
Document Information
Modified date:
14 March 2025
UID
ibm16597977