Troubleshooting
Problem
How do I determine the event that is causing the system notification message "Unable to determine associated log source" (QID 38750007)
Symptom
Tip: SIEM administrators can run a search for the system notification QID 38750007 - for example as a weekly audit to determine what new event sources might need manual log sources or a DSM Editor updates.
System notifications are all outlined as part of the QRadar system notifications guide.
- Procedure
To complete a search for the event that triggered this warning.- Log in to the QRadar Console.
- From the navigation bar, click the bell icon for notifications.
- Hover over the Unable to determine associated log source for IP address system notification for the details of the event.
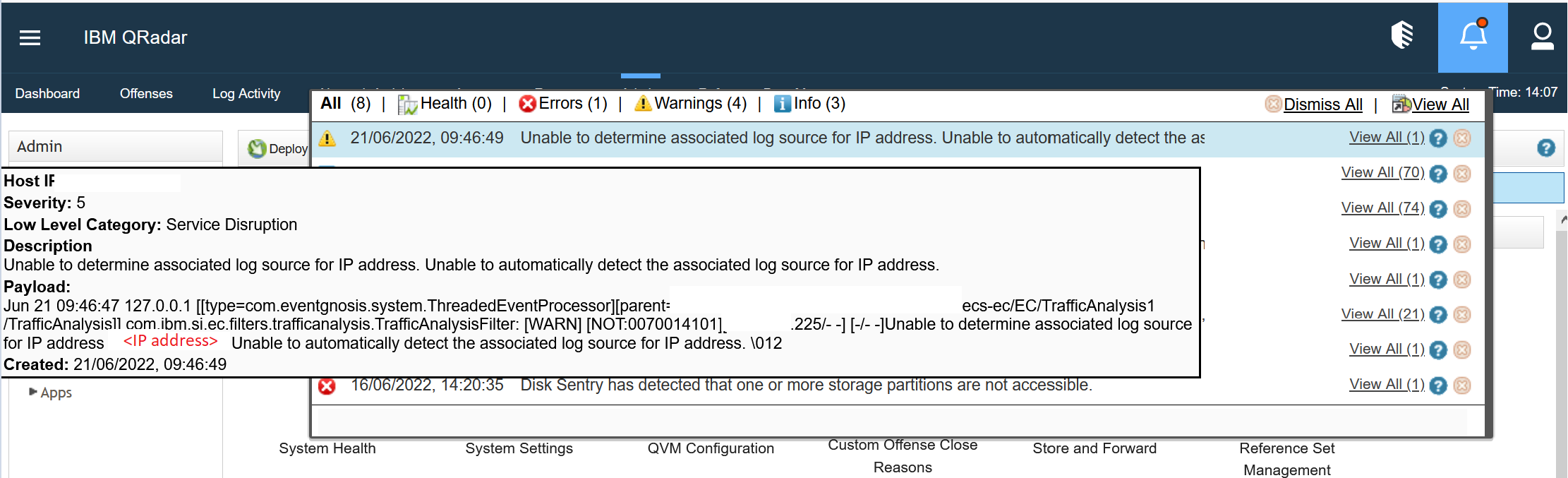
- The highlighted IP address is the address for the event source, which an administrator would use in their investigation of why the log source was unable to parse.
Document Location
Worldwide
[{"Type":"MASTER","Line of Business":{"code":"LOB77","label":"Automation Platform"},"Business Unit":{"code":"BU048","label":"IBM Software"},"Product":{"code":"SSBQAC","label":"IBM Security QRadar SIEM"},"ARM Category":[{"code":"a8m0z000000cwt0AAA","label":"Log Source"}],"ARM Case Number":"","Platform":[{"code":"PF025","label":"Platform Independent"}],"Version":"All Versions"},{"Type":"MASTER","Line of Business":{"code":"LOB77","label":"Automation Platform"},"Business Unit":{"code":"BU048","label":"IBM Software"},"Product":{"code":"SSYS0N","label":"IBM QRadar SIEM (SaaS)"},"ARM Category":[{"code":"a8m0z000000cwt0AAA","label":"Log Source"}],"Platform":[{"code":"PF025","label":"Platform Independent"}],"Version":""}]
Log InLog in to view more of this document
This document has the abstract of a technical article that is available to authorized users once you have logged on. Please use Log in button above to access the full document. After log in, if you do not have the right authorization for this document, there will be instructions on what to do next.
Was this topic helpful?
Document Information
Modified date:
24 June 2022
UID
ibm16586500