Troubleshooting
Problem
The option, "Ensure the detected event is part of an offense" does not prevent events from being added to the new offense when the rule has a stateful.
Symptom
Offenses generated by stateful rules include both CRE events and events detected by the tests when the wanted behavior is to include CRE events only.
A stateful rule is one such as "when at least this many events are seen with the same event properties in this many minutes"
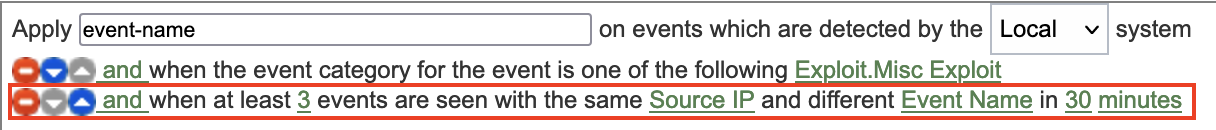
Example of an affected rule:
We show how to apply the work-around to this affected rule in the Resolving the Problem section.
- Rule tests:
- when the event category for the event is one of the following Exploit.Misc Exploit
- when at least 3 events are seen with the same Source IP and different Event Name in 30 minutes
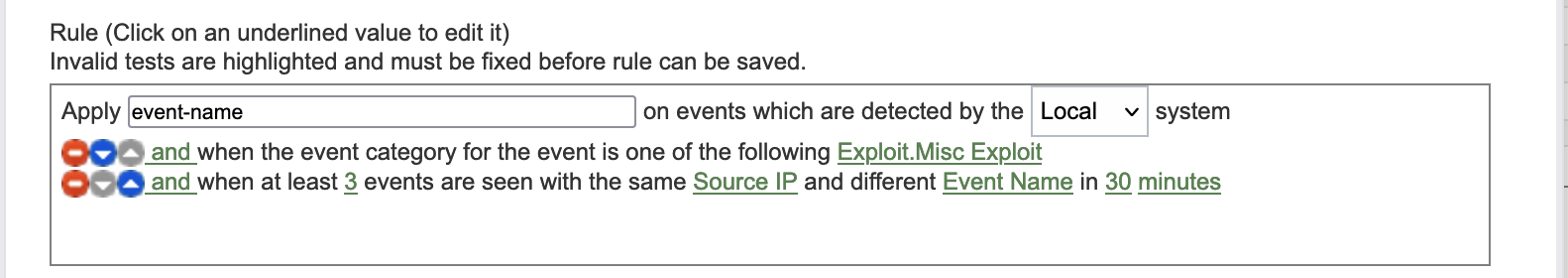
- Rule Action: Do not check "Ensure the detected event is part of an offense"
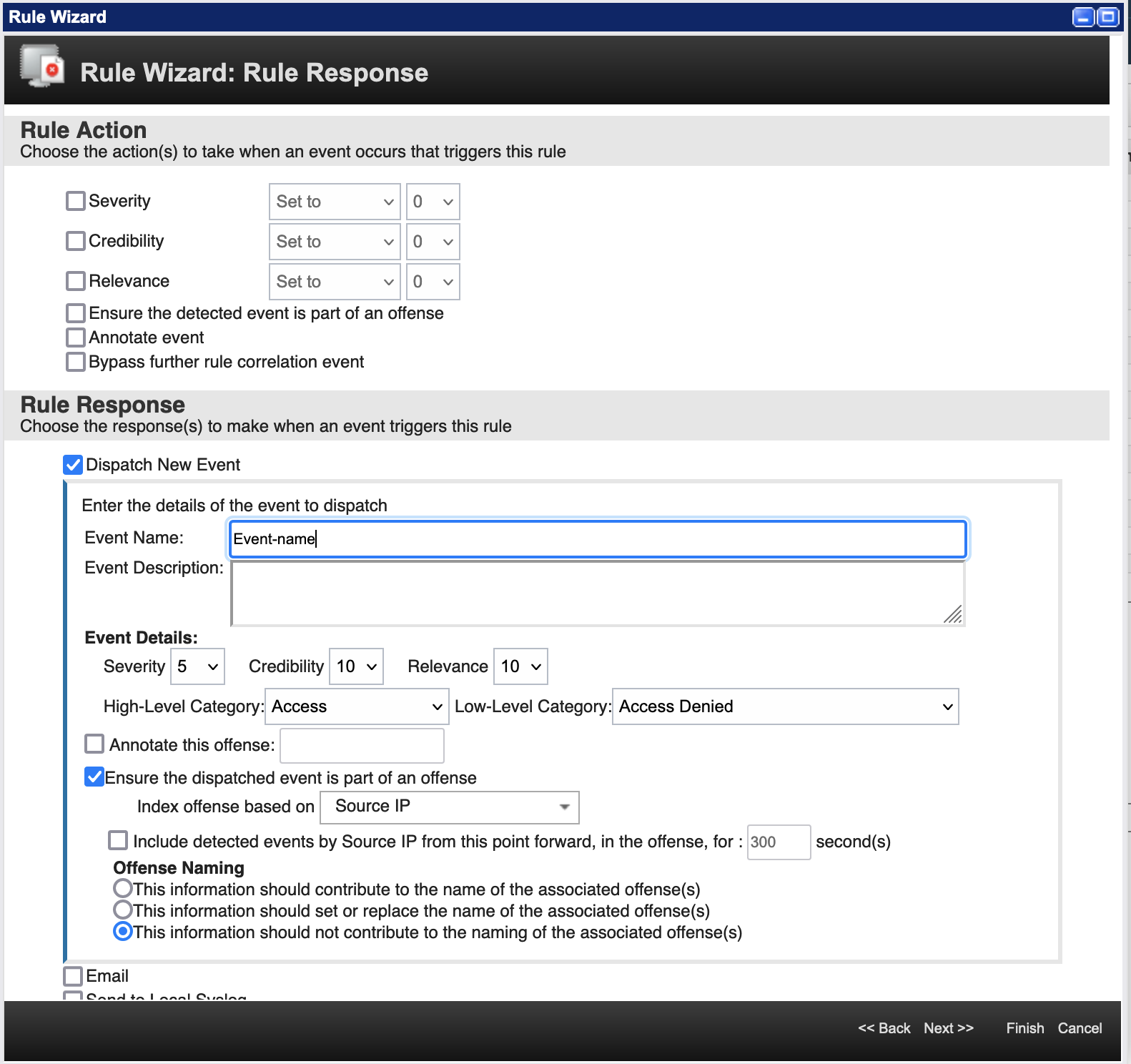
- Rule Response: Check "Dispatch New Event" and "Ensure the dispatched event is part of an offense"
Document Location
Worldwide
[{"Type":"MASTER","Line of Business":{"code":"LOB77","label":"Automation Platform"},"Business Unit":{"code":"BU048","label":"IBM Software"},"Product":{"code":"SSBQAC","label":"IBM Security QRadar SIEM"},"ARM Category":[{"code":"a8m0z000000cwtrAAA","label":"Rules"}],"ARM Case Number":"TS007811578","Platform":[{"code":"PF025","label":"Platform Independent"}],"Version":"All Versions"}]
Log InLog in to view more of this document
This document has the abstract of a technical article that is available to authorized users once you have logged on. Please use Log in button above to access the full document. After log in, if you do not have the right authorization for this document, there will be instructions on what to do next.
Was this topic helpful?
Document Information
Modified date:
25 April 2022
UID
ibm16567811