News
Abstract
The IWS server has been enhanced in the area of authentication by allowing for the definition of a user-defined authentication mechanism called the trust association interceptor (TAI).
Content
You are in: IBM i Technology Updates > Welcome to IBM Integrated Web Services for i Technology Updates > Trust authentication interceptor
What is it?
When a web service is protected using basic authentication, but selected requests do not present the required credential, a trust association interceptor (TAI) can be developed, configured, and deployed in the server to allow selected "unauthenticated" requests to be processed.
For example, where an API gateway component has already authenticated requests that presented a credential, and no associated credential is available for the onward request to the server, a TAI can be developed to identify such requests and allow them to be processed under a fixed application or task identity. Requests that do not match the criteria of the TAI must still present the required credential to proceed. The criteria by which a TAI decides to block or allow a request is entirely due to the design of the TAI implementation.
The web administration GUI has been enhanced to show the following panel for configuring a TAI:
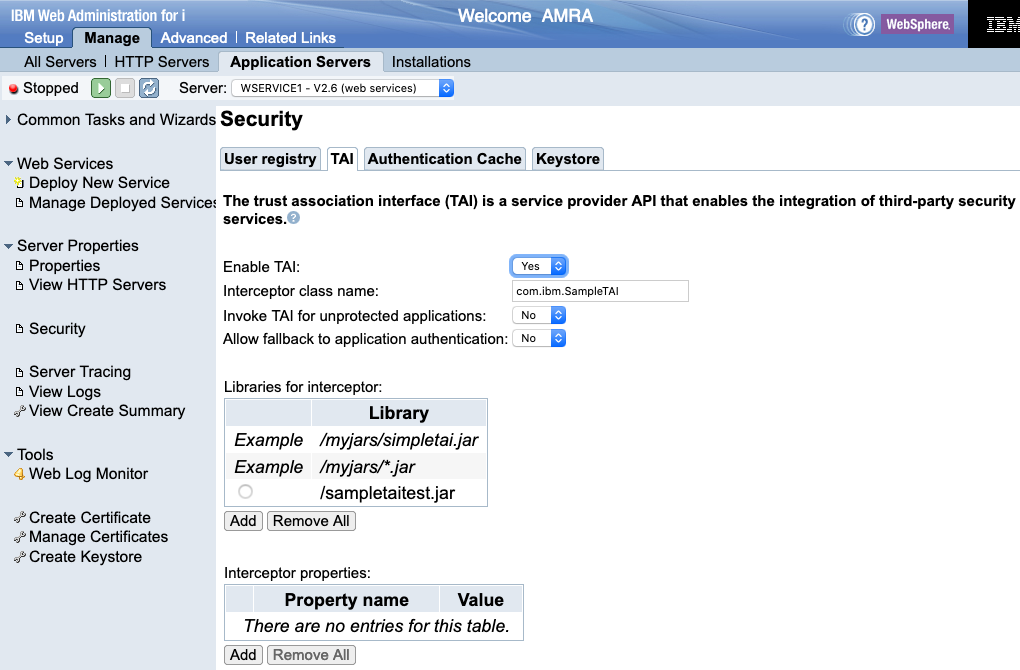
- Interceptor class name. In order to configure a TAI, you need specify a fully qualified package name of the interceptor class.
- Invoke TAI for unprotected applications. Whether the TAI should be invoked for all web services or just for protected web services.
- Allow fallback to application authentication. Whether to fall back to application authentication (assuming it is protected) if the TAI fails to authenticate.
- Libraries for interceptor. The JAR file that contains the TAI, in addition to any additional libraries that the TAI is depends on.
- Interceptor properties. Properties that are to be passed to the TAI.
Changes to the user TAI configuration require the server to be in a stopped state.
Here is a sample TAI class called SimpleTAI, which also lists all available methods from the TrustAssociationInterceptor interface:
package com.ibm.websphere.security.sample;
import java.util.Properties;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import com.ibm.websphere.security.WebTrustAssociationException;
import com.ibm.websphere.security.WebTrustAssociationFailedException;
import com.ibm.wsspi.security.tai.TAIResult;
import com.ibm.wsspi.security.tai.TrustAssociationInterceptor;
public class SimpleTAI implements TrustAssociationInterceptor
{
public SimpleTAI()
{
super();
}
public boolean isTargetInterceptor(HttpServletRequest req)
throws WebTrustAssociationException
{
//Add logic to determine whether to intercept this request
return true;
}
public TAIResult negotiateValidateandEstablishTrust(HttpServletRequest req,
HttpServletResponse resp) throws WebTrustAssociationFailedException
{
// Add logic to authenticate a request and return a TAI result.
String tai_user = "taiUser";
return TAIResult.create(HttpServletResponse.SC_OK, tai_user);
}
public int initialize(Properties arg0) throws WebTrustAssociationFailedException
{
return 0;
}
public String getVersion()
{
return "1.0";
}
public String getType()
{
return this.getClass().getName();
}
public void cleanup() { }
}
Note: When running IWS 2.0, you are running Java EE. IWS 3.0 or newer versions run Jakarta EE, thus you will need to specify Jakarta EE packages. In particular, the following packages must be changed:
javax.servlet.http.HttpServletRequest -->
javax.servlet.http.HttpServletRequest -->
jakarta.servlet.http.HttpServletRequest and javax.servlet.http.HttpServletResponse --> jakarta.servlet.http.HttpServletResponse.When processing the web request, the server calls out and passes the HttpServletRequest and HttpServletResponse to the trust association interceptor. The HttpServletRequest calls the isTargetInterceptor method of the interceptor to see whether the interceptor can process the request. After a trust association interceptor is selected, the HttpServletRequest is processed by the negotiateValidateandEstablishTrust method of the interceptor, and the result is returned in a TAIResult object. You can add your own logic code to each method of the custom TAI class.
To compile the code, you need the following (xx is some number):
- /QIBM/ProdData/OS/ApplicationServer/runtime/wlp/dev/api/ibm/com.ibm.websphere.appserver.api.security_1.3.xx.jar
- /QIBM/ProdData/OS/ApplicationServer/runtime/wlp/dev/api/ibm/com.ibm.websphere.appserver.api.securityClient_1.1.xx.jar
See also the Java API document for the TAI interface. The Java API documentation for each Liberty API is detailed in the Programming interfaces (Javadoc) section of the online IBM Documentation. (See Programming interfaces -> Liberty API -> WebSphere Security API, package com.ibm.wsspi.security.tai).
Why use it?
To authenticate users using third-party security services.
Availability
The support is enabled in the following HTTP group PTFs and PTFs:
V7R2M0 SF99713 Level 40, SI75444, SI75178
V7R3M0 SF99722 Level 28, SI75443, SI75177
V7R4M0 SF99662 Level 09, SI75442, SI75176
[{"Business Unit":{"code":"BU058","label":"IBM Infrastructure w\/TPS"},"Product":{"code":"HW1A1","label":"IBM Power Systems"},"Component":"","Platform":[{"code":"PF012","label":"IBM i"}],"Version":"All Versions","Edition":"","Line of Business":{"code":"LOB57","label":"Power"}}]
Was this topic helpful?
Document Information
Modified date:
29 April 2026
UID
ibm16396908