Technical Blog Post
Abstract
Maximo and LDAP - Configuration from Start to Finish
Body
Security is more important than ever, and securing applications is a priority to every company. Many clients ask for documentation on configuring Maximo for LDAP authentication. You end up having to review many different articles to address a single topic, this document lays out a basic LDAP configuration that uses WebSphere 7 through 9.0.5 and Maximo 7.5.0.5 and later. This document walks through connecting WebSphere to your domain right down to the synchronization process and hopefully give a clearer understanding of the configuration process. For this blog, we are going to discuss this configuration with Microsoft Active Directory (MSAD or AD). However, these steps can be applied with Tivoli Directory Server as well.
So, where do you start?
Your first thoughts are who need access to Maximo and how are we going to filter just these users into the environment. For our purpose here, we're going to restrict all users with the memberOf attribute, and make sure our Maximo users are members of a maximousers group that are filtered on.
For a new Maximo implementation, we need three users to exist in the directory
- Maxadmin – default administrative user
- Maxreg – default user registration security user
- Mxintadm – default integration framework user
You can use different usernames for these administrative users. The user must match these conditions:
- The user is in the Maximo database.
- The username (MAXUSER.LOGINID) must match an account with the same Common Name (CN) or uid in Active Directory.
- The user must be in the maximousers group.
(Note that User synchronization with VMMSYNC or LDAPSYNC is not required to change administrative users.)
Now to get started with your configuration. When Maximo for LDAP is configured, there are three parts.
Step 1: Configure WebSphere to connect and authenticate against your directory server
Step 2: Enable Maximo to authenticate logins with the Federated Repository, the user database maintained in WebSphere Application Server)
Step 3: Configure Maximo to synchronize users from the Federated Repository configured in WebSphere, which contains the users that are brought over from Active Directory.
Step 1: Configuring WebSphere
-
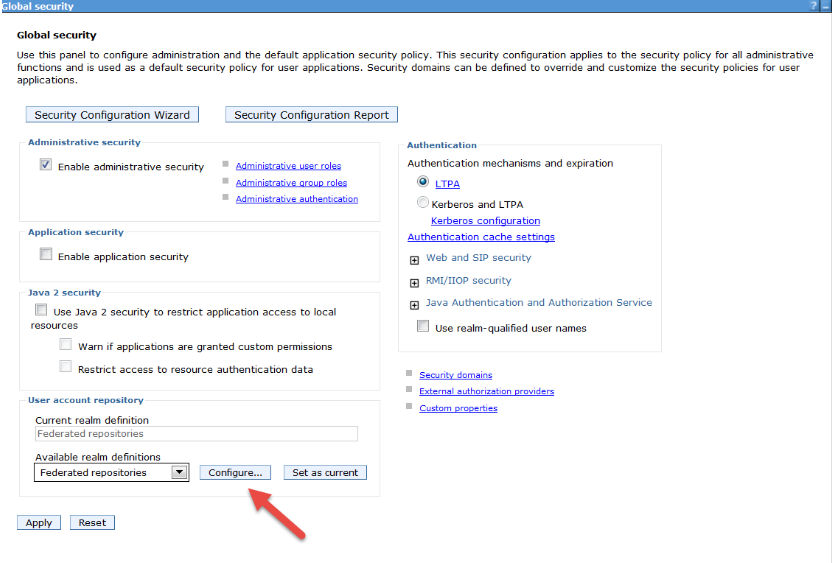
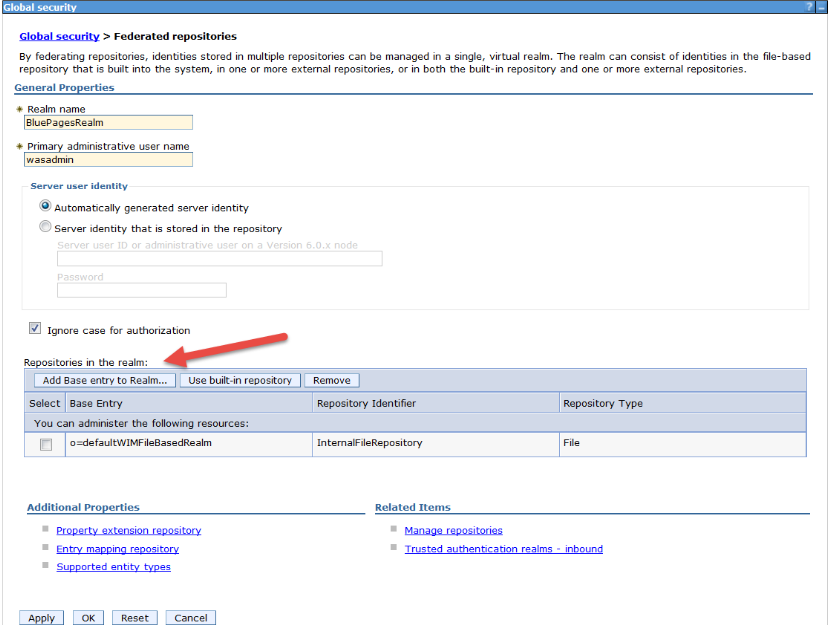
From the WebSphere Console, expand Security in the left frame and click Global Security. From the Global Security page, choose Federated Repository as your available realm definitions and click configure.
2. Once you click Configure, you are in the federated repositories page. This page shows the current repositories configured with WebSphere. By default the repository called InternalFileRepository exists. This repository contains the wasadmin user and its group. For this tutorial, we are going to leave it intact so that the wasadmin DOES NOT need to be added to the directory server. Click Manage Repositories to configure your realm.
Note – if wasadmin exists on your directory server you need to remove the file-based realm or remove wasadmin from the realm.
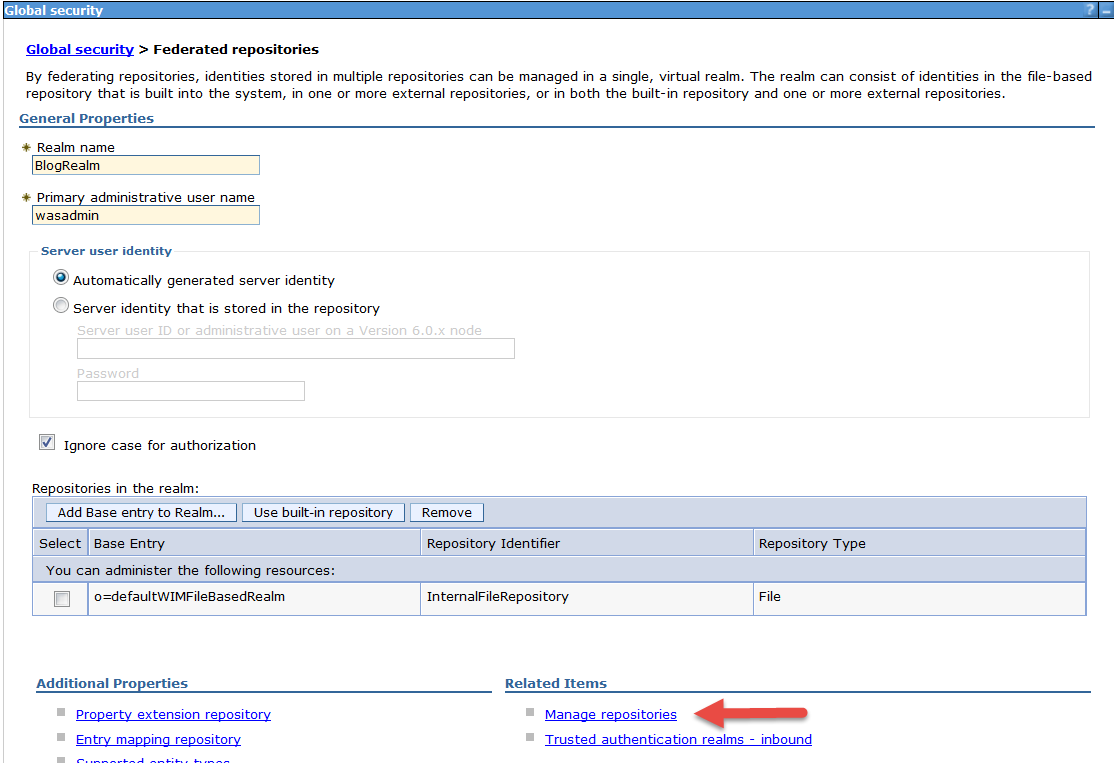
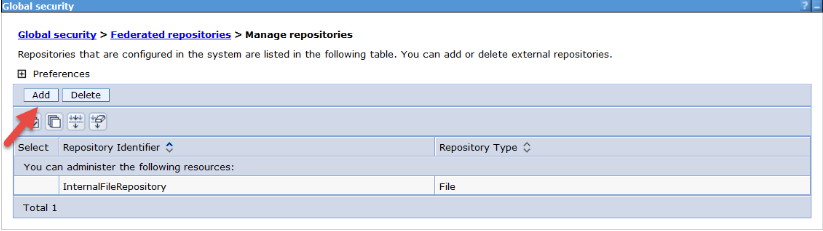
3. From the Manage Repositories screen, click Add
-
Once you click add, you are brought to the properties page to configure your directory server. From the drop-down menu, choose your directory type; here we chose Active Directory. Enter the hostname and port of your directory server and your principal user to make the connection between WebSphere and your directory. I created a user named “principal” for this purpose.
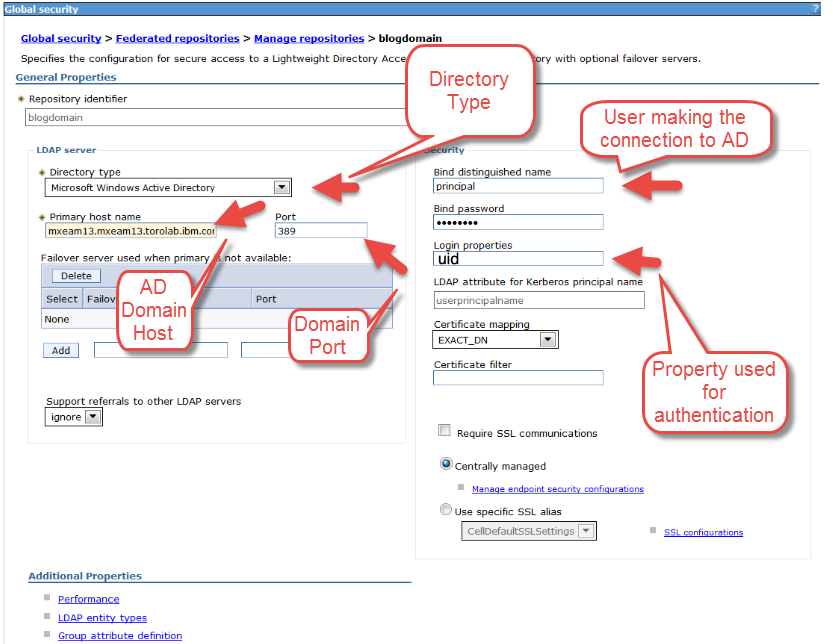
For Active Directory, we changed the login property to uid. The WebSphere uid property maps to sAMAccountName in Active Directory. It would be left as uid for IBM Directory Services. Once done, click Apply and Save to the master configuration.
4. Once you saved to the master configuration, you are brought back to the Manage Repositories screen that shows your newly created repository. From here, head back to the main configuration screen for the repository by clicking “Federated Repositories.”

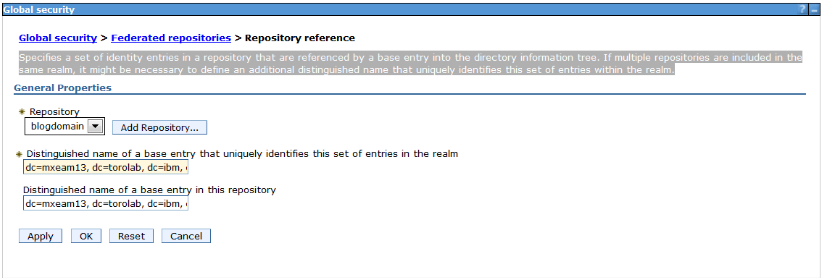
5. Now we need to configure our base entries. This repository is the container that WebSphere looks in on your directory for users and groups. You can configure multiple entries on this screen, but we are just going to point our realm to the top of the directory. To start click Add Base Entry to Realm.
6. From the Add Base Entry screen, enter the DN you want WebSphere to look in, as mentioned earlier we are going to pull in the entire domain and filter at the Maximo level. So I entered dc=mxeam13, dc=torolab, dc=ibm, dc=com for the top level of the domain. Once done, click apply and save to your master configuration.
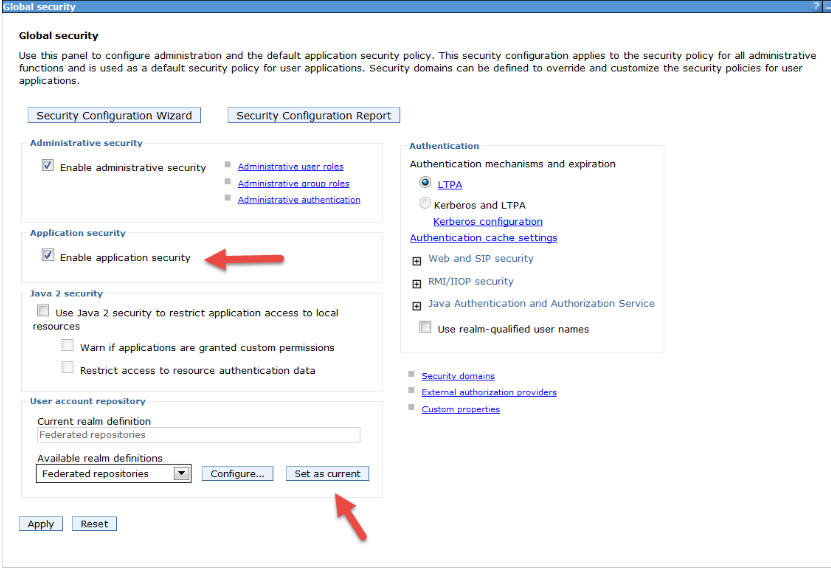
7. Once you have your Base entries configured, you need to enable application security for WebSphere. You do it on the main Global Security page. Check 'Enable Application Security' and click 'Set as current' so your Current Realm Definition becomes Federated Repositories. Then, apply and save to the master configuration.
8. Now that your configuration is complete for WebSphere, you need to do a full node synchronization and restart your Deployment Manager (dmgr) and Node (node agent) Windows services before the Maximo configuration is continued.
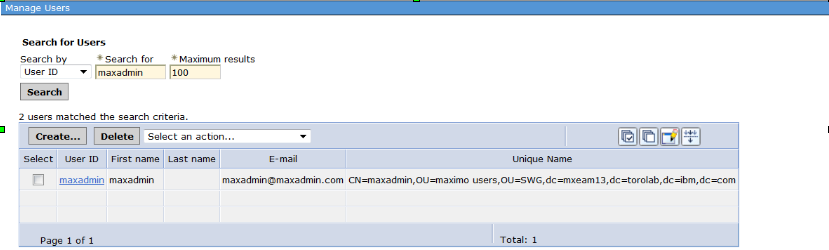
9. Once you restarted your services, log in to the WebSphere Console. On the left side, expand Users and Groups and click Manage Users. Search for a known directory user to confirm that your configuration is correct
Step 2: Enabling Maximo authenticate against your directory server
Once WebSphere is configured for LDAP authentication, we need to configure Maximo. It is done by enabling LDAP security in 4 XML files as well as the maximo.properties file or the maxpropvalue table.
-
The first XML file we modify is the maximouiweb web.xml. By default, you find it in \ibm\smp\maximo\applications\maximo\maximouiweb\webmodule\WEB-INF\web.xml.
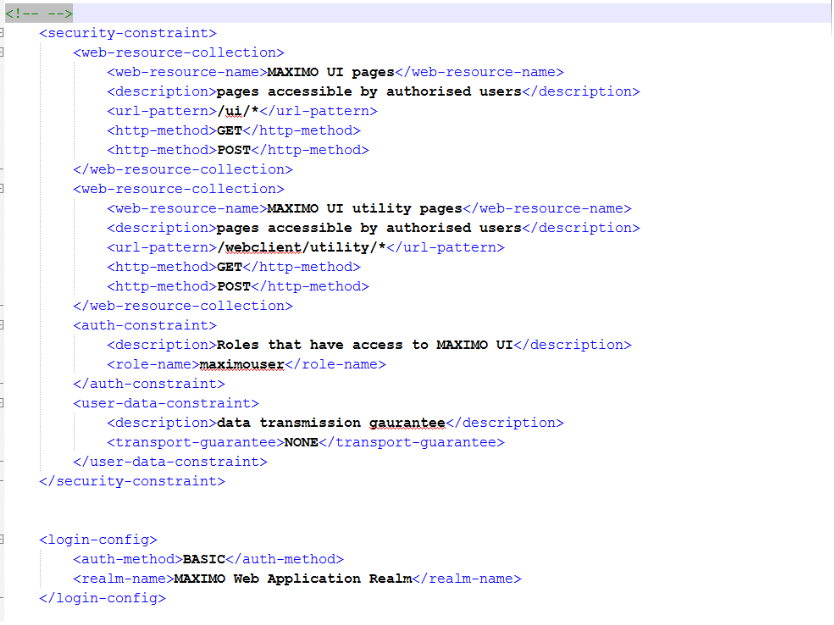
We first want to search for the <security-constraint> tag and uncomment to the end of </login-config> as shown here:
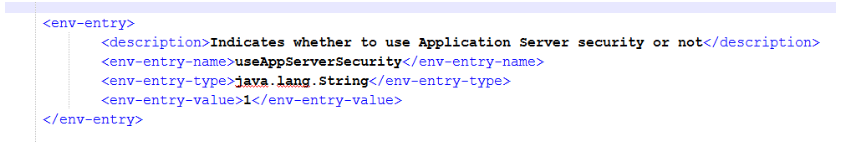
2. In the same file search for useAppServerSecurity, and change the value from false to 1 as follows:
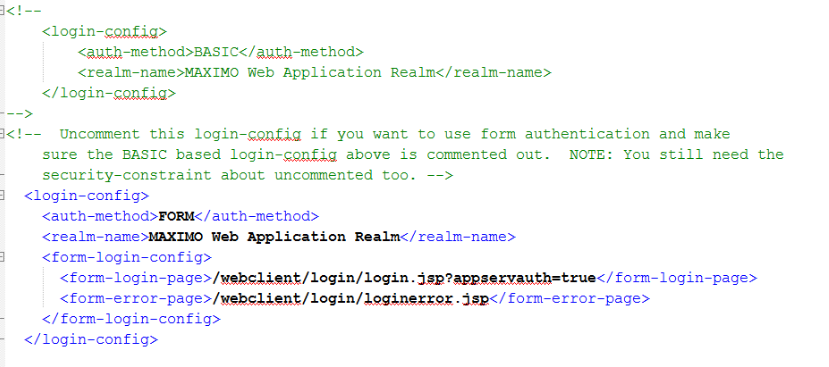
3. If you want to keep the BASIC authentication method, you can now save the file. If you want Maximo to display the normal login screen, you need to update the file to use FORM authentication, by commenting out the BASIC login config and uncommenting the FORM login-config. Here, text in green is the commented-out section:
4. Repeat this step without the auth-method in the following 3 web.xml files – that is, uncomment the <security-constraint> sections and change useAppServerSecurity=1:
- IBM\SMP\maximo\applications\maximo\mboweb\webmodule\WEB-INF
- IBM\SMP\maximo\applications\maximo\meaweb\webmodule\WEB-INF
- IBM\SMP\maximo\applications\maximo\maxrestweb\webmodule\WEB-INF
-
Now that your web.xml files are configured for LDAP we need to update the maximo.properties or the maxpropvalue table for application security.
To enable Application Server Security in the database, update the property value with the following statement in an SQL tool connected to your database as the schema owner (default maximo):
update maxpropvalue set propvalue=1 where propname='mxe.useAppServerSecurity';
Once your file changes are made, you can rebuild and redeploy your ear files
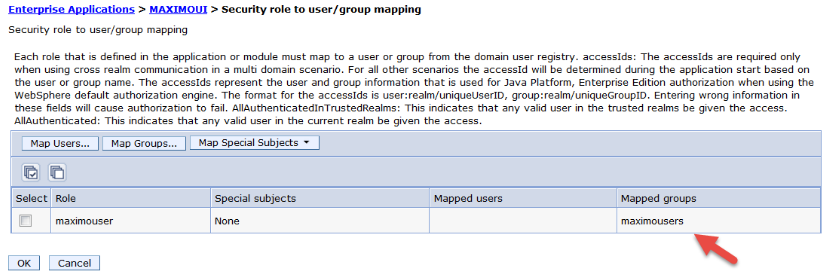
5. Before the application is started, you need to map the security role to the group of users you want to authenticate. Our users are part of the maximousers group, so we already mapped that role. If you don't have a specific group, you can choose “All Authenticated in Applications realm” to give all authenticated directory users the ability to connect to Maximo.
To map your role from the WebSphere console, click Enterprise Applications then on your Maximo ear. Under Detail properties, click security role to user/group mapping. Then, click Map Groups to map the groups your users are contained in.
Step 3. Configure Maximo to synchronize users from your repository.
Our final step is to create the VMMSYNC crontask instance to bring users in to Maximo from the directory server.
-
Open System Configuration - > Platform Configuration and click crontask set up. From here filter for VMMSYNC.
-
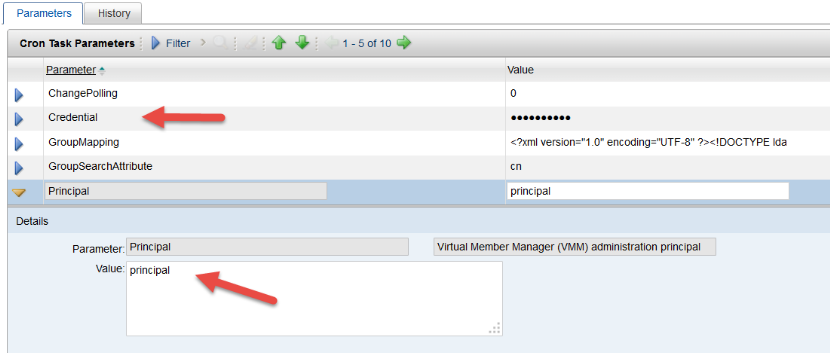
Enter the principal user that can access the repository to bring users into Maximo as well as the password for this user in the credential field.
3. Once your credentials are set up, you can set up your group mapping to sync the groups you want into Maximo.
4. Between the <basedn></basedn> tags, specify the path on your directory to where your groups reside. In our case it is in the SWG OU, see the example as follows:
<basedn>ou=SWG, dc=mxeam13, dc=torolab, dc=ibm, dc=com</basedn>
5. However, next, we need to do the same for our users, at the same time we are just bringing in users that are members of the maximousers group.
<basedn>ou=SWG, dc=mxeam13, dc=torolab, dc=ibm, dc=com</basedn>
<filter>PersonAccount' and memberof='cn=maximousers, ou=SWG, ou=maximo groups, dc=torolab, dc=ibm, dc=com</filter>
6. Once these changes are done, activate your crontask and reload its configuration. If you are having problems with the memberOf filter, it is likely because it doesn't exist as a property under the PersonAccount entity in the repository. You can add it using the instructions as follows:
Adding the memberof to the PersonAccount entity in VMM
From IBM\
Once the wsadmin command line displays, run the following command
Linux:
$AdminTask addIdMgrPropertyToEntityTypes {-name memberof -dataType string -entityTypeNames PersonAccount}
Windows:
$AdminTask.addIdMgrPropertyToEntityTypes ('[-name memberof -dataType string -entityTypeNames PersonAccount]'
-name: The name of the attribute on the Directory Server. In this case, it is memberof
-dataType: The database for the field, in this string
After the command is run, your attribute was successfully added
7. Synchronize the nodes and restart the services. See Manually synchronizing WebSphere Application Server nodes for instructions.
Your synchronization is now able to use memberof as a filter.
UID
ibm11133001