Technical Blog Post
Abstract
IBM Decision Optimization Center - setting up the application server for SSL connections from Maximo Scheduler
Body
While my colleague was working on installing and setting up Maximo Scheduler to connect to and use IBM Decision Optimization Center (DOC) running as an application deployed within a WebSphere application server container, it was determined that the Scheduler application can only connect to the DOC application using a secure connection (TLS). Since the setup of TLS can be confusing, I have put together the steps I used to create the digital certificate for the ODME server, and configure the ODME application server to be able it to use the new certificate. Once this configuration was completed, the Maximo Scheduler application could connect securely to the DOC application server.
Here are my steps.
The following assumes you have already patched your WebSphere applciation server to the latest version 8.5.5.X and configured your WebSphere application server to use TLS1.2 to protect against any security vulnerabilities. Information on performing these steps can be found in the following document links:
https://developer.ibm.com/answers/questions/206952/how-do-i-configure-websphere-application-server-ss.html
These are the steps I used to create the configuration and certificate for the DOC server.
1. Create a new SSL configuration
Navigate in the WAS console to Security/SSL Certificate and key management.
On the right side of the screen, click SSL Configurations.
Click the New button to create a new configuration.
In the name field, enter the name you want to use for this configuration. I used the name ODMESSLCONFIG as shown here:
Set the Trust store name to CellDefaultTrustStore and the Keystore name to NodeDEfaultKeyStore.
Set the management scope to the Node scope where the keystore is visible and apply the changes. The certificate for this server has not yet been created so we do not need to set any default aliases yet.
Synchronize all changes.
2. Create a new Certificate
Now that we have a new configuration we can use for the DOC server, on the right select "Keystores and Certificates".
Click the NodeDefaultKeyStore.
On the right side of the screen, Personal Certificates.
Click the Create button and Notice there are three choices. We will be creating a self-signed certificate for this configuration. If you wish to use a Certificate Authority signed certificate, you will create a CA-Signed Certificate request here and submit it to the CA to be signed and returned. For the purposes of this document, we will be using a self-signed certificate.
Select Self-signed Certificate from the Create dropdown.
Create the alias you would like to use to help you identify this certificate. For this certificate, I used "odmepc".
For this environment, I created a 2048 bit ke and used the SHA256withRSA signature algorithm.
Apply the changes and synchronize your nodes.
3. Extract the public key from your certificate
Now navigate back to your list of personal certificates.
Select the checkbox beside your new certificate called odmepc and click the Extract button.
In certificate filename, enter the name of the file in which you want to save the copy of the extracted certificate and save it.
I used odme.cer, and saved it as the Base64 encoded data type.
The file will be saved in the working directory of the application server.
4. Add the cacerts Java key store to the WebSphere console
The Maximo Scheduler application requires the extracted certificate to be added to its trust stores in order to be able to validate the certificate received from the DOC server during the connection handshake.
The extracted certificate should be added to *all* client trust stores that need to be able to connect to the DOC server. This can include browsers or other tools you may have that connect to the DOC application server instance.
Maximo Scheduler uses the cacerts file included with the WebSphere Java installation where the Maximo Scheduler application runs when connecting as a client to the DOC server. This is a JKS (java) key store. This key store is not managed by WebSphere by default so we need to add it to the console simply for ease of adding the certificate as a trusted signer to it.
To ensure all components worked correctly, I added the extracted certificate to the CellDefaultTrustStore and the WAS_INSTALL_ROOT/AppServer/java/jre/lib/security/cacerts file. Both can be done using the WebSphere console. But first we need to make the cacerts file accessible in the console.
To do this, navigate to your SSL configuration and then to Keystores and Certificates.
Click the New button to add a new keystore:
The absolute path is required to tell the server where the existing keystore is.
Ensure that you select JKS as the keystore type.
The default password for existing cacerts key stores is:
changeit
Save and apply the changes. Synchronize your nodes.
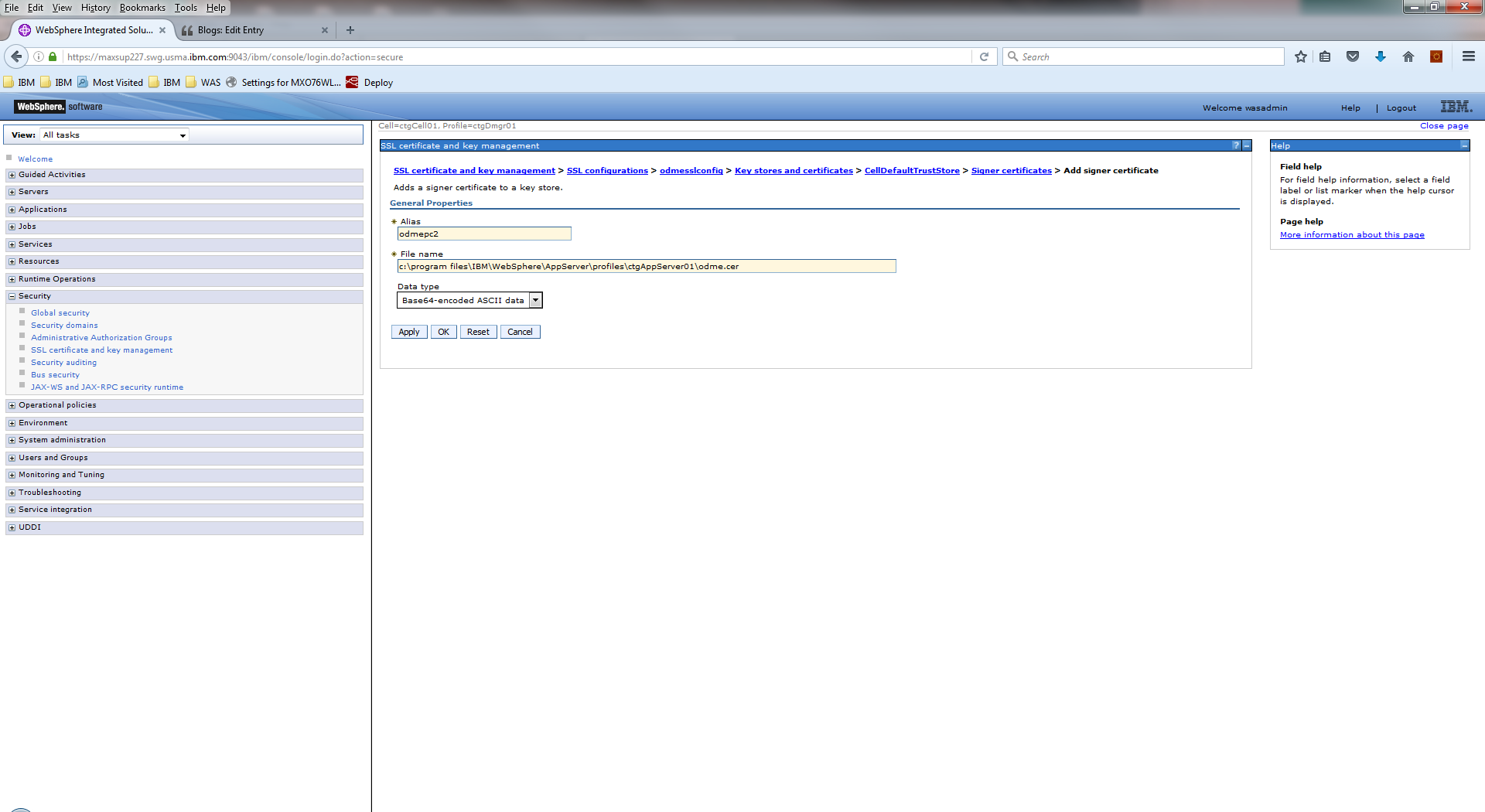
5. Add the extracted certificate as a trusted signer
Now we can add the extracted certificate to both the CellDefaultTrustStore and the cacerts stores as a trusted signer using the WebSphere console.
Navigate to the cacerts keystore, and on the right side of the screen, select Signers.
Enter an alias for the extracted certificate. I called it:
odmepcroot
Enter the full path to the odme.cer file extracted earlier, then click the Apply button.
The certificate will look something like this:
The above output indicates the signer was added to the keystore.
Repeat these steps for the CellDefaultTrustStore file as shown below:
Save and synchronize the changes.
6. Update the SSL configuration to use the new certificate
Now we need to update the SSL configuration created earlier so that it uses the new certificate as its default certificate.
Navigate to your SSL configuration and click the button Get Certificate Aliases
This will populate the default client and server aliases. Select the certificate alias from the list, and apply the changes.
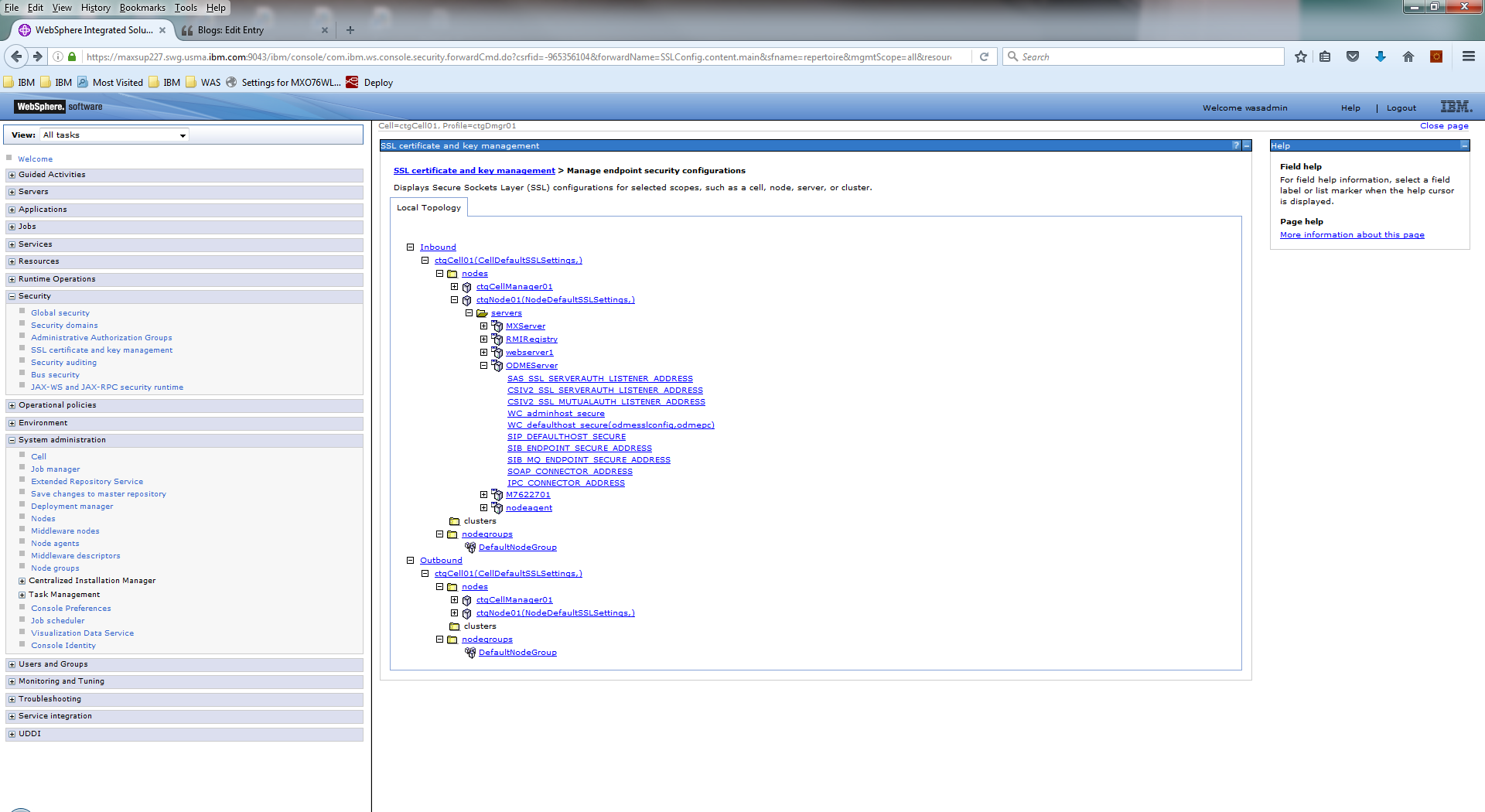
7. Update the DOC server instance to use the new SSL configuration and certificate
Now we need to then we need to tell the DOC application server to use this SSL configuration for communications.
Navigate to Security/ssl certificates and key management
On the main page, click the link Manage Endpoint Security Configurations.
Navigate to your DOC server instance under the "inbound" hierarchy path.
Click on wc_defaulthost_secure.
Select the checkbox Override Interited Values.
In the dropdown, select your new ssl configuration. Once you select your configuration, you can select Update Certificate Alias List which will update the list of available certificate aliases in this configuration. In the certificate alias dropdown, select your alias.
Apply the changes, then restart the application servers as well as all WebSphere components to be sure the new certificate has been picked up.
8. Add the certificate to any other clients that need to connect to the DOC server instance
Don't forget to add this certificate to your browser's trust stores to connect to your DOC server using your new certificate.
Maximo Scheduler should now be able to connect to the DOC server instance securely.
UID
ibm11131099