Troubleshooting
Problem
This document includes steps to configure the IBM i FTP server to use TLS.
Resolving The Problem
This document includes steps to configure the iSeries FTP server to use TLS.
Use the following steps to configure the iSeries FTP server to use TLS. This document was created under the assumption that the user has already accessed Digital Certificate Manager (DCM) and has already either purchased a third-party certificate, or has created their own certificate to assign to the FTP server.
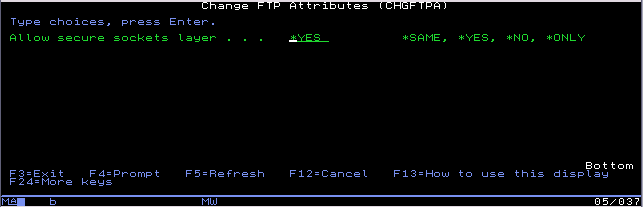
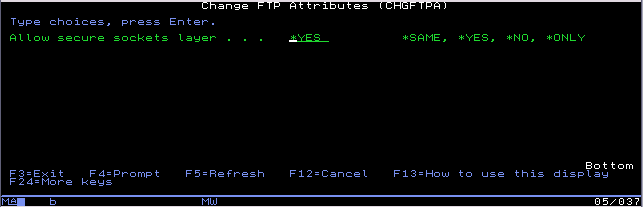
1. In the CHGFTPA screen (F4 to prompt this command), set the Allow secure sockets layer option to *YES. The *ONLY option will also allow TLS FTP connections; however, it will not allow regular non-secure connections to come through. After making the change, restart the FTP server (ENDTCPSVR *FTP and then STRTCPSVR *FTP).
2. Go to the Digital Certificate Manager application to assign a certificate to the FTP server application ID. You will need to make sure the HTTP Admin server is active and that it can be accessed. In the QHTTPSVR subsystem, there should be an ADMIN job. If Admin is not active, use the command STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN) to start it. The Admin page can be accessed by going to http://<systemname or IP address>:2001/dcm

3. Click on the 'Open Certificate Store' link and choose the *SYSTEM store. Enter your store password when it prompts you (this was created by the individual who created the *SYSTEM store).
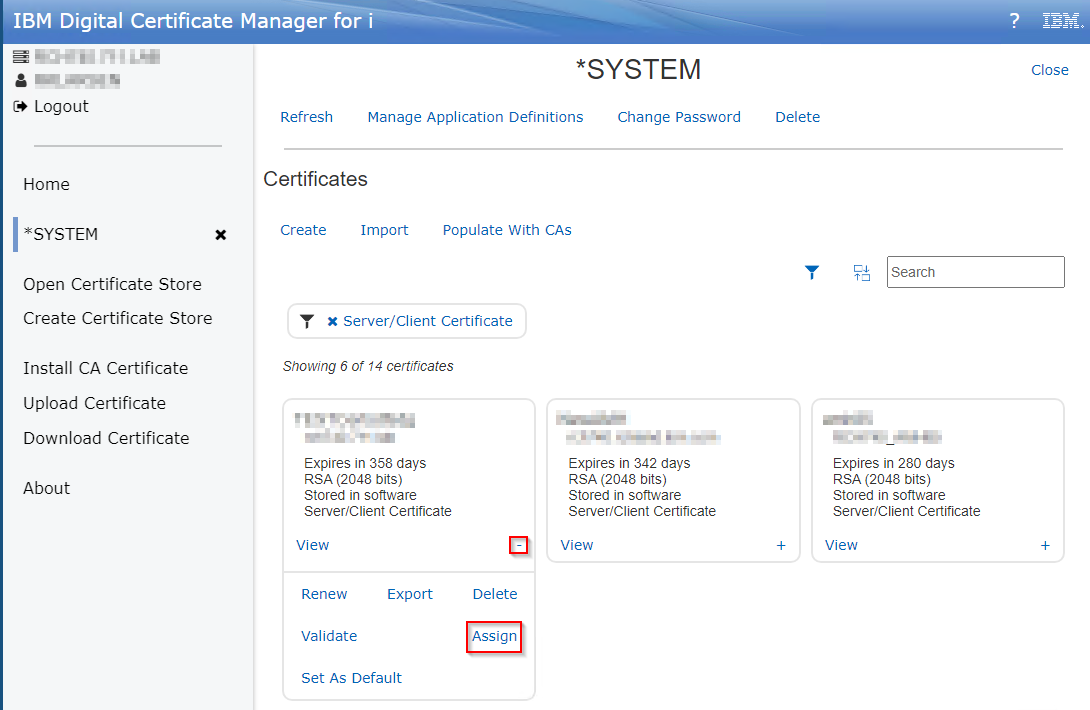
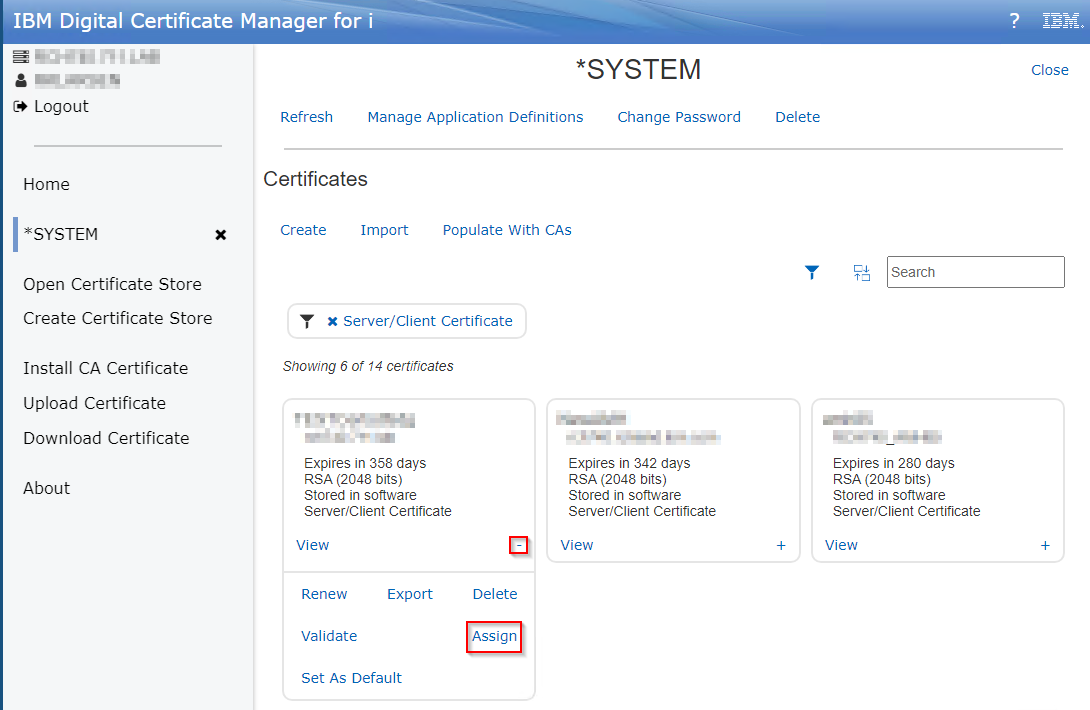
4. Once you are signed in you will be presented with a list of Server/Client certificates. Locate the certificate tile you would like to assign to the FTP server and click on the + in the bottom right of the tile, then click 'Assign'
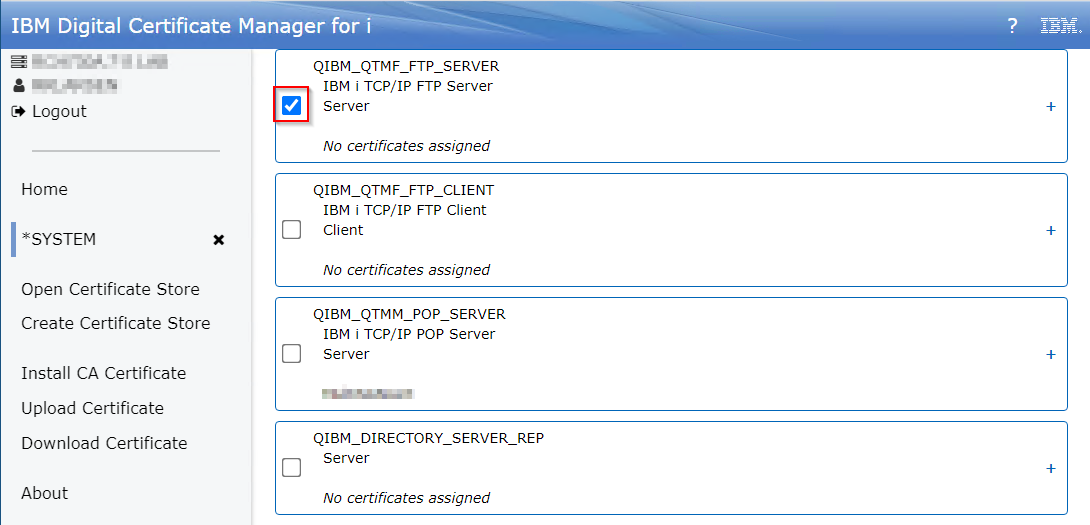
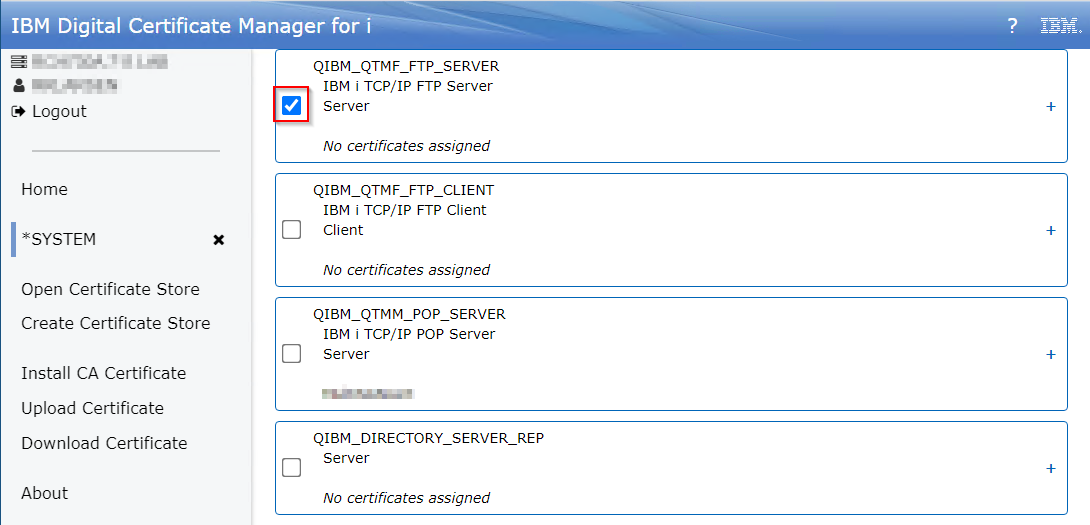
5. Check the box for IBM i TCP/IP FTP Server and click Replace either at the top or the bottom of the screen.
6. You should receive a green success message in the top right indicating that the certificate has been assigned:

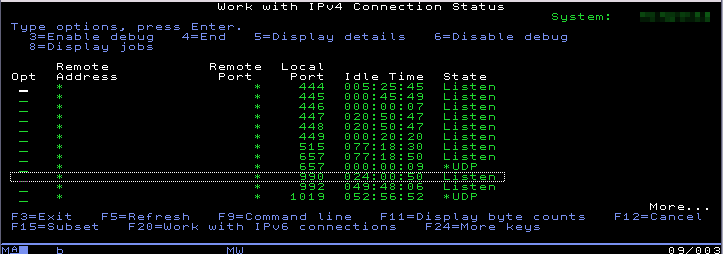
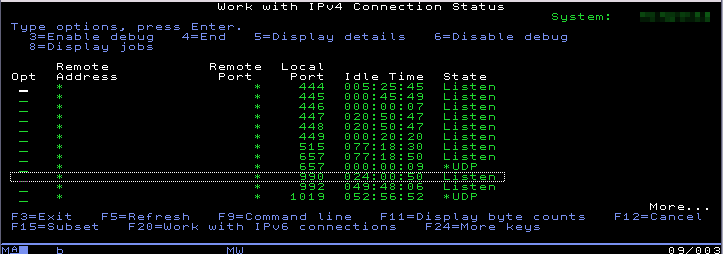
7. Restart the FTP server application ENDTCPSVR *FTP and then STRTCPSVR *FTP. Check NETSTAT option 3 to verify the FTP secure port is listening. You can use F13 to sort by local port and then F14 to display the local port to make it easier to find port 990 (the secure FTP listener).
Anyone who wants to connect to the FTP server securely will likely need the CA (Certificate Authority) of the certificate that was used to secure the FTP server. You can export this CA and send it to whomever requires it.
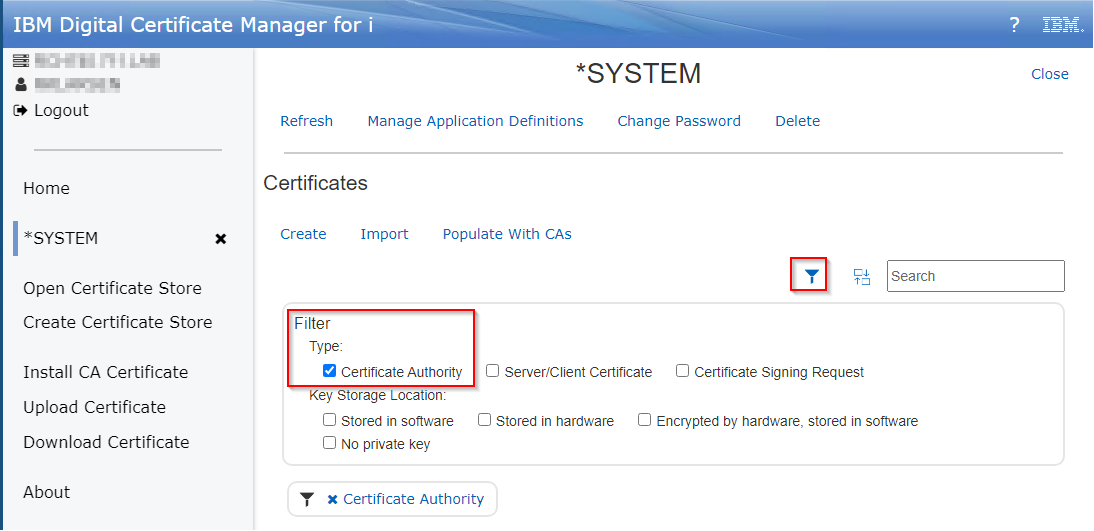
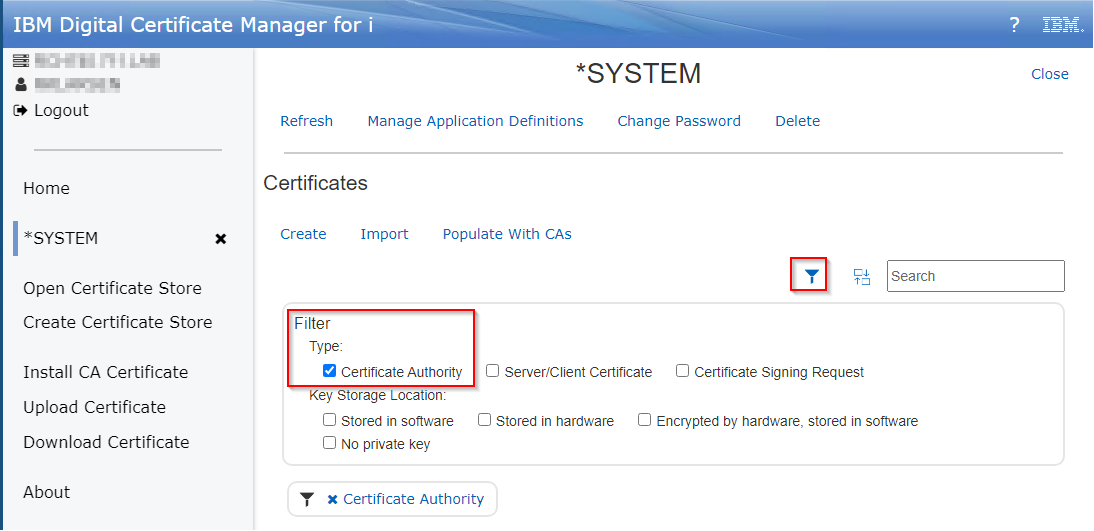
8. In DCM again, click on the filter button on the right and select 'Certificate Authority':
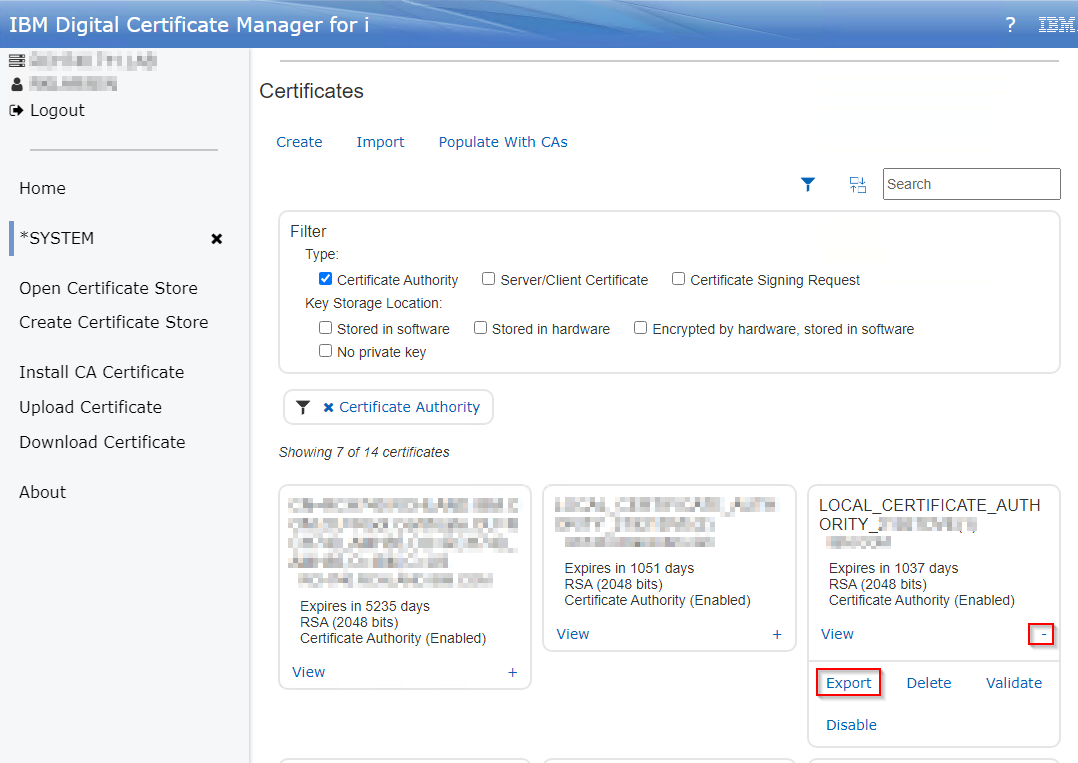
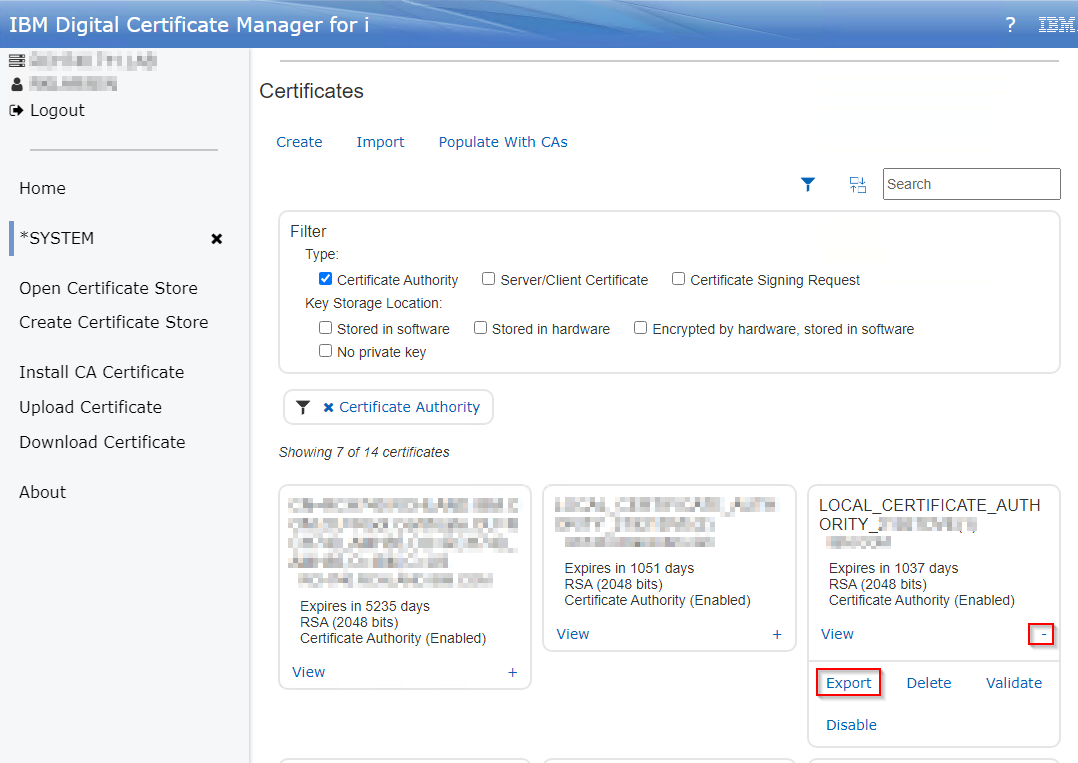
9. Click the + in the bottom right of the Certificate Authority tile, then click Export. If it was a locally signed certificate, you will see LOCAL_CERTIFICATE_AUTHORITY:
10. Under 'Location' click the File link.
11. Fill in the Path: field then click 'Export'. This file will go to the IFS, and you must include the path and name of the file you are creating. For example, to export to your personal home directory in the IFS, you would specify /home/username/cert.cer where username is your User profile directory and cert.cer is whatever you want to call the certificate file. The extension can be .txt, .cer, .crt, or just about whatever you choose. Note: Windows OS recognizes the .cer extension as a certificate and is probably a good choice to use.

12. Send the file to whomever requires it. You may need to move the file to your PC if you do not have software to send it directly from the i5.
The client will then import the CA to whatever application they use for client side FTP. They can then attempt to connect to the FTP server securely.
Use the following steps to configure the iSeries FTP server to use TLS. This document was created under the assumption that the user has already accessed Digital Certificate Manager (DCM) and has already either purchased a third-party certificate, or has created their own certificate to assign to the FTP server.
1. In the CHGFTPA screen (F4 to prompt this command), set the Allow secure sockets layer option to *YES. The *ONLY option will also allow TLS FTP connections; however, it will not allow regular non-secure connections to come through. After making the change, restart the FTP server (ENDTCPSVR *FTP and then STRTCPSVR *FTP).
2. Go to the Digital Certificate Manager application to assign a certificate to the FTP server application ID. You will need to make sure the HTTP Admin server is active and that it can be accessed. In the QHTTPSVR subsystem, there should be an ADMIN job. If Admin is not active, use the command STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN) to start it. The Admin page can be accessed by going to http://<systemname or IP address>:2001/dcm

3. Click on the 'Open Certificate Store' link and choose the *SYSTEM store. Enter your store password when it prompts you (this was created by the individual who created the *SYSTEM store).
4. Once you are signed in you will be presented with a list of Server/Client certificates. Locate the certificate tile you would like to assign to the FTP server and click on the + in the bottom right of the tile, then click 'Assign'
5. Check the box for IBM i TCP/IP FTP Server and click Replace either at the top or the bottom of the screen.
6. You should receive a green success message in the top right indicating that the certificate has been assigned:

7. Restart the FTP server application ENDTCPSVR *FTP and then STRTCPSVR *FTP. Check NETSTAT option 3 to verify the FTP secure port is listening. You can use F13 to sort by local port and then F14 to display the local port to make it easier to find port 990 (the secure FTP listener).
Anyone who wants to connect to the FTP server securely will likely need the CA (Certificate Authority) of the certificate that was used to secure the FTP server. You can export this CA and send it to whomever requires it.
8. In DCM again, click on the filter button on the right and select 'Certificate Authority':
9. Click the + in the bottom right of the Certificate Authority tile, then click Export. If it was a locally signed certificate, you will see LOCAL_CERTIFICATE_AUTHORITY:
10. Under 'Location' click the File link.
11. Fill in the Path: field then click 'Export'. This file will go to the IFS, and you must include the path and name of the file you are creating. For example, to export to your personal home directory in the IFS, you would specify /home/username/cert.cer where username is your User profile directory and cert.cer is whatever you want to call the certificate file. The extension can be .txt, .cer, .crt, or just about whatever you choose. Note: Windows OS recognizes the .cer extension as a certificate and is probably a good choice to use.

12. Send the file to whomever requires it. You may need to move the file to your PC if you do not have software to send it directly from the i5.
The client will then import the CA to whatever application they use for client side FTP. They can then attempt to connect to the FTP server securely.
[{"Type":"MASTER","Line of Business":{"code":"LOB57","label":"Power"},"Business Unit":{"code":"BU058","label":"IBM Infrastructure w\/TPS"},"Product":{"code":"SWG60","label":"IBM i"},"ARM Category":[{"code":"a8m0z0000000CLbAAM","label":"Communications-\u003EFTP"},{"code":"a8m0z0000000CSxAAM","label":"Digital Certificate Manager-\u003EFAQs"}],"ARM Case Number":"","Platform":[{"code":"PF012","label":"IBM i"}],"Version":"7.3.0;7.4.0;7.5.0"}]
Historical Number
522844747
Was this topic helpful?
Document Information
Modified date:
12 August 2022
UID
ibm16610369